The Infisical Mongo Atlas dynamic secret allows you to generate Mongo Atlas Database credentials on demand based on configured role.Documentation Index
Fetch the complete documentation index at: https://infisical.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
Prerequisite
Create a project scoped API Key with the required permission in your Mongo Atlas following the official doc.The API Key must have permission to manage users in the project.
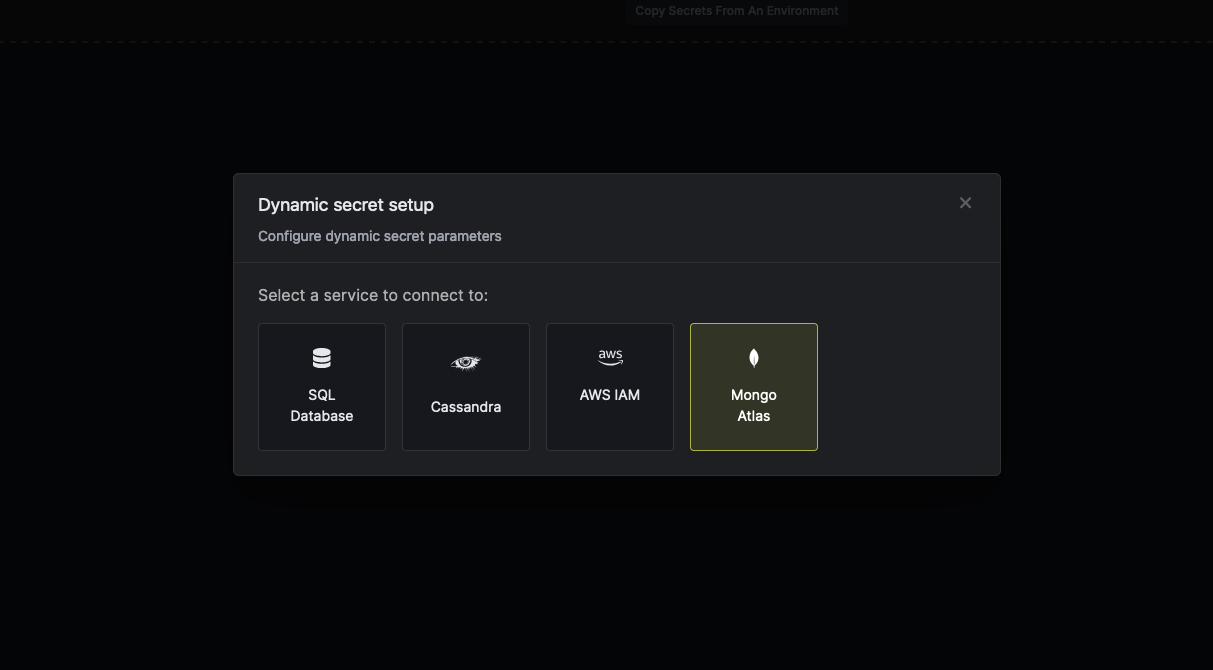
Set up Dynamic Secrets with Mongo Atlas
Open Secret Overview Dashboard
Open the Secret Overview dashboard and select the environment in which you would like to add a dynamic secret.
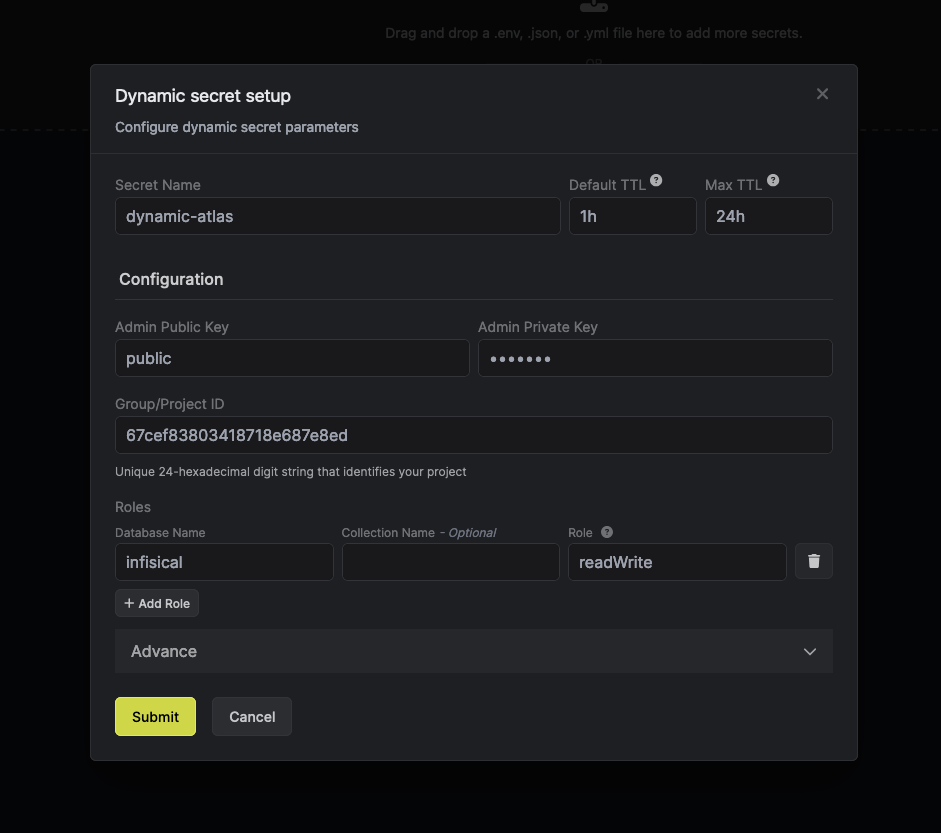
Provide the inputs for dynamic secret parameters
Name by which you want the secret to be referenced
Default time-to-live for a generated secret (it is possible to modify this value after a secret is generated)
Maximum time-to-live for a generated secret
The public key of your generated Atlas API Key. This acts as a username.
The private key of your generated Atlas API Key. This acts as a password.
Unique 24-hexadecimal digit string that identifies your project. This is same as project id
List that provides the pairings of one role with one applicable database.
- Database Name: Database to which the user is granted access privileges.
- Collection: Collection on which this role applies.
- Role Name: Human-readable label that identifies a group of privileges assigned to a database user. This value can either be a built-in role or a custom role.
- Enum:
atlasAdminbackupclusterMonitordbAdmindbAdminAnyDatabaseenableShardingreadreadAnyDatabasereadWritereadWriteAnyDatabase<a custom role name>.
- Enum:
(Optional) Modify Access Scope
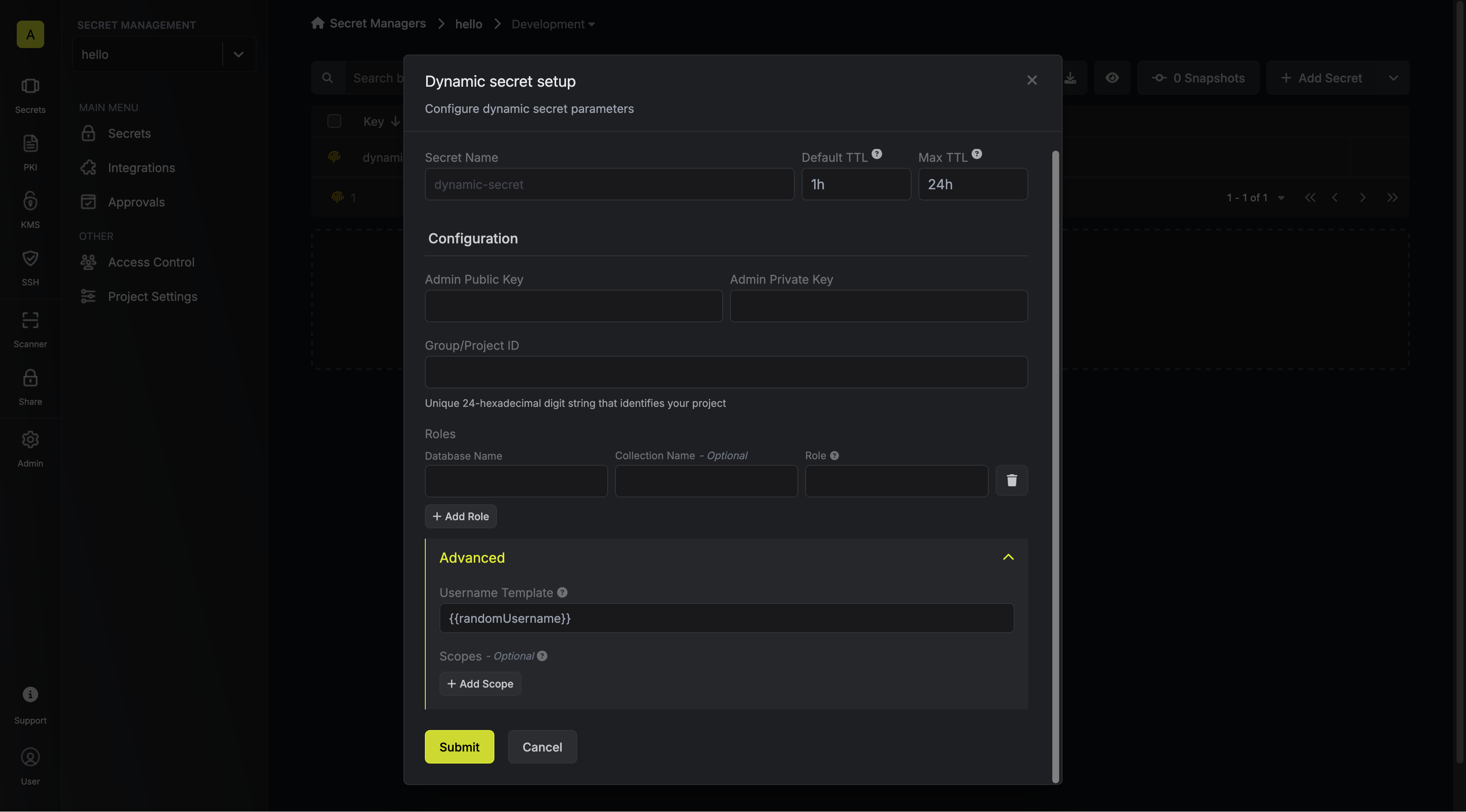
Specifies a template for generating usernames. This field allows customization of how usernames are automatically created.Allowed template variables are:
{{randomUsername}}: Random username string.{{unixTimestamp}}: Current Unix timestamp at the time of lease creation.{{identity.name}}: Name of the identity that is generating the lease.{{dynamicSecret.name}}: Name of the associated dynamic secret.{{dynamicSecret.type}}: Type of the associated dynamic secret.{{random N}}: Random string of N characters.
truncate: Truncates a string to a specified length.replace: Replaces a substring with another value.uppercase: Converts a string to uppercase.lowercase: Converts a string to lowercase.
List that contains clusters, MongoDB Atlas Data Lakes, and MongoDB Atlas Streams Instances that this database user can access. If omitted, MongoDB Cloud grants the database user access to all the clusters, MongoDB Atlas Data Lakes, and MongoDB Atlas Streams Instances in the project.
- Label: Human-readable label that identifies the cluster or MongoDB Atlas Data Lake that this database user can access.
- Type: Category of resource that this database user can access.
Click 'Submit'
After submitting the form, you will see a dynamic secret created in the dashboard.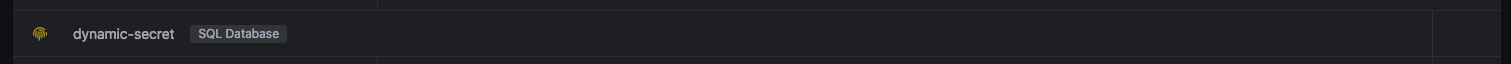
If this step fails, you may have to add the CA certificate.
Generate dynamic secrets
Once you’ve successfully configured the dynamic secret, you’re ready to generate on-demand credentials.
To do this, simply click on the ‘Generate’ button which appears when hovering over the dynamic secret item.
Alternatively, you can initiate the creation of a new lease by selecting ‘New Lease’ from the dynamic secret lease list section.
 When generating these secrets, it’s important to specify a Time-to-Live (TTL) duration. This will dictate how long the credentials are valid for.
When generating these secrets, it’s important to specify a Time-to-Live (TTL) duration. This will dictate how long the credentials are valid for. Once you click the
Once you click the 

 When generating these secrets, it’s important to specify a Time-to-Live (TTL) duration. This will dictate how long the credentials are valid for.
When generating these secrets, it’s important to specify a Time-to-Live (TTL) duration. This will dictate how long the credentials are valid for. Once you click the
Once you click the Submit button, a new secret lease will be generated and the credentials for it will be shown to you.
Audit or Revoke Leases
Once you have created one or more leases, you will be able to access them by clicking on the respective dynamic secret item on the dashboard. This will allow you to see the expiration time of the lease or delete a lease before it’s set time to live.
Renew Leases
To extend the life of the generated dynamic secret leases past its initial time to live, simply click on the Renew button as illustrated below.