In certain situations, developers need to expand their access to a certain new project or a sensitive environment. For those use cases, it is helpful to utilize Infisical’s Access Requests functionality.Documentation Index
Fetch the complete documentation index at: https://infisical.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
Access Requests is a paid feature.If you’re using Infisical Cloud, then it is available under the Pro Tier and Enterprise Tier.
If you’re self-hosting Infisical, then you should contact sales@infisical.com to purchase an enterprise license to use it.
Overview
Access Requests allow users to request temporary or permanent access to secrets in specific environments and folders. Administrators can define policies that control who can approve requests, set time limits, and configure expiration rules.Creating Access Policies
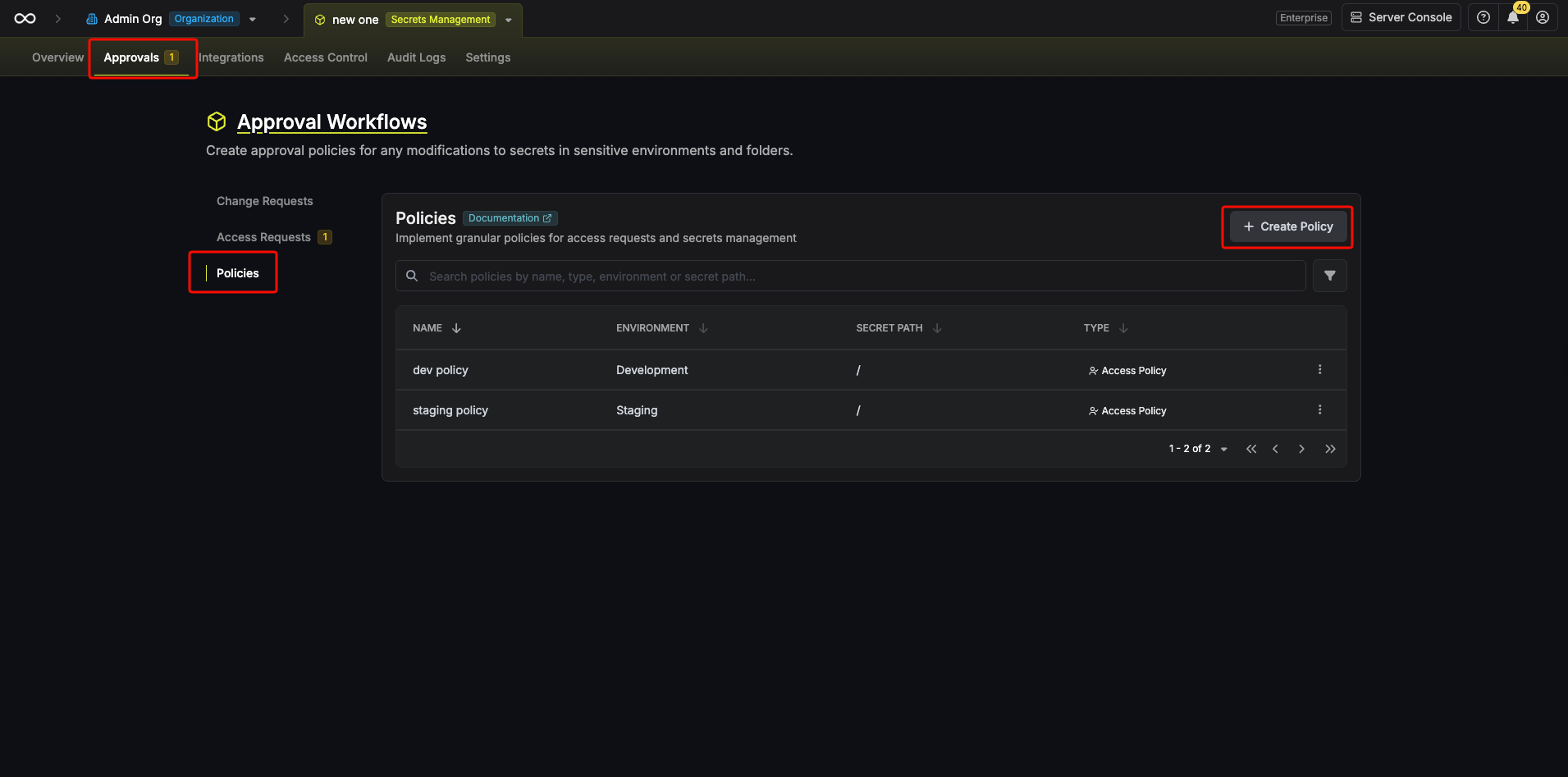
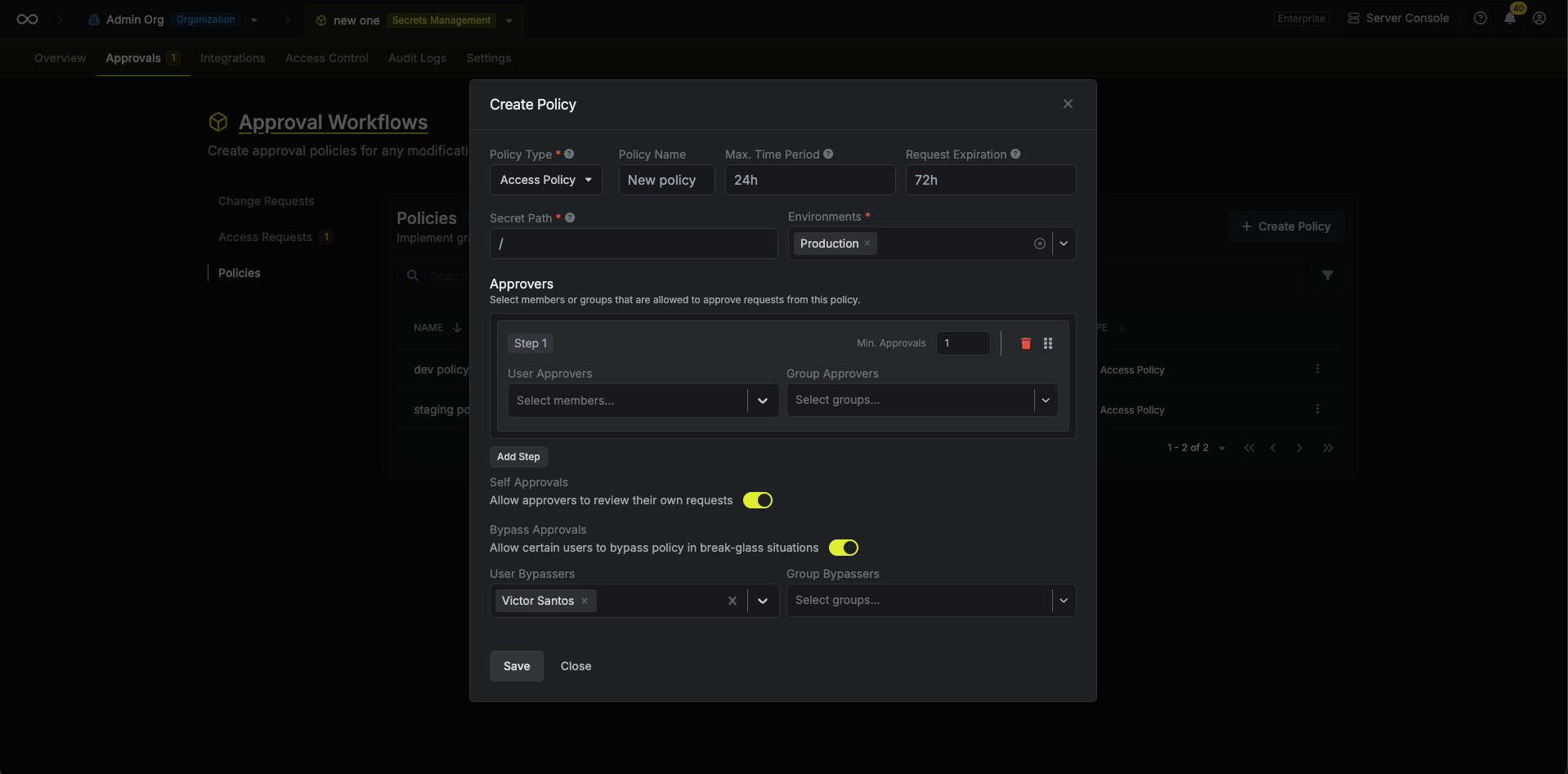
Before users can submit access requests, a project administrator must create an Access Policy that defines the approval workflow.Setting Up an Access Policy
- In a Secrets Management project, navigate to the Approvals tab and then the Policies menu in the sidebar.
- Click Create Policy and select Access Policy as the policy type.
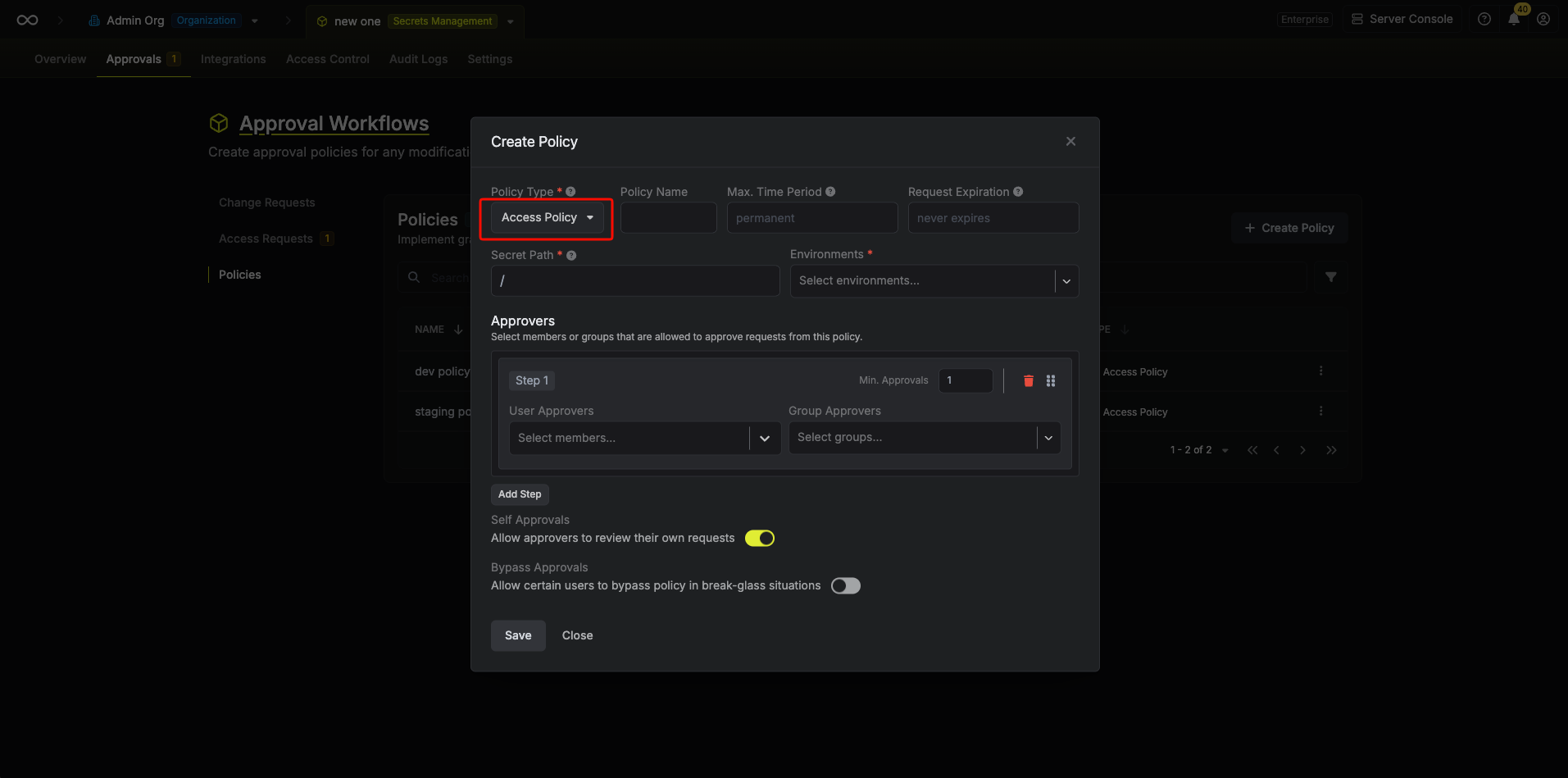
Policy Configuration Options
| Option | Description |
|---|---|
| Policy Name | A descriptive name for the policy (e.g., “Production Access Policy”). |
| Max Time Period | The maximum duration a user can request access for (e.g., 1h, 3d, 1w). Leave empty or set to “permanent” to allow permanent access requests. |
| Request Expiration | Time before unapproved requests automatically expire (e.g., 24h, 3d, 72h). Expired requests are moved to the Closed tab and cannot be approved. Leave empty or set to “never” for requests that never expire. |
| Secret Path | The folder path this policy governs. Supports glob patterns (e.g., /** for all paths, /api/* for specific folders). |
| Environments | One or more environments this policy applies to (e.g., Production, Staging). |
Multi-Step Approval Workflows
Access policies support sequential multi-step approval workflows where approvals must follow a designated chain.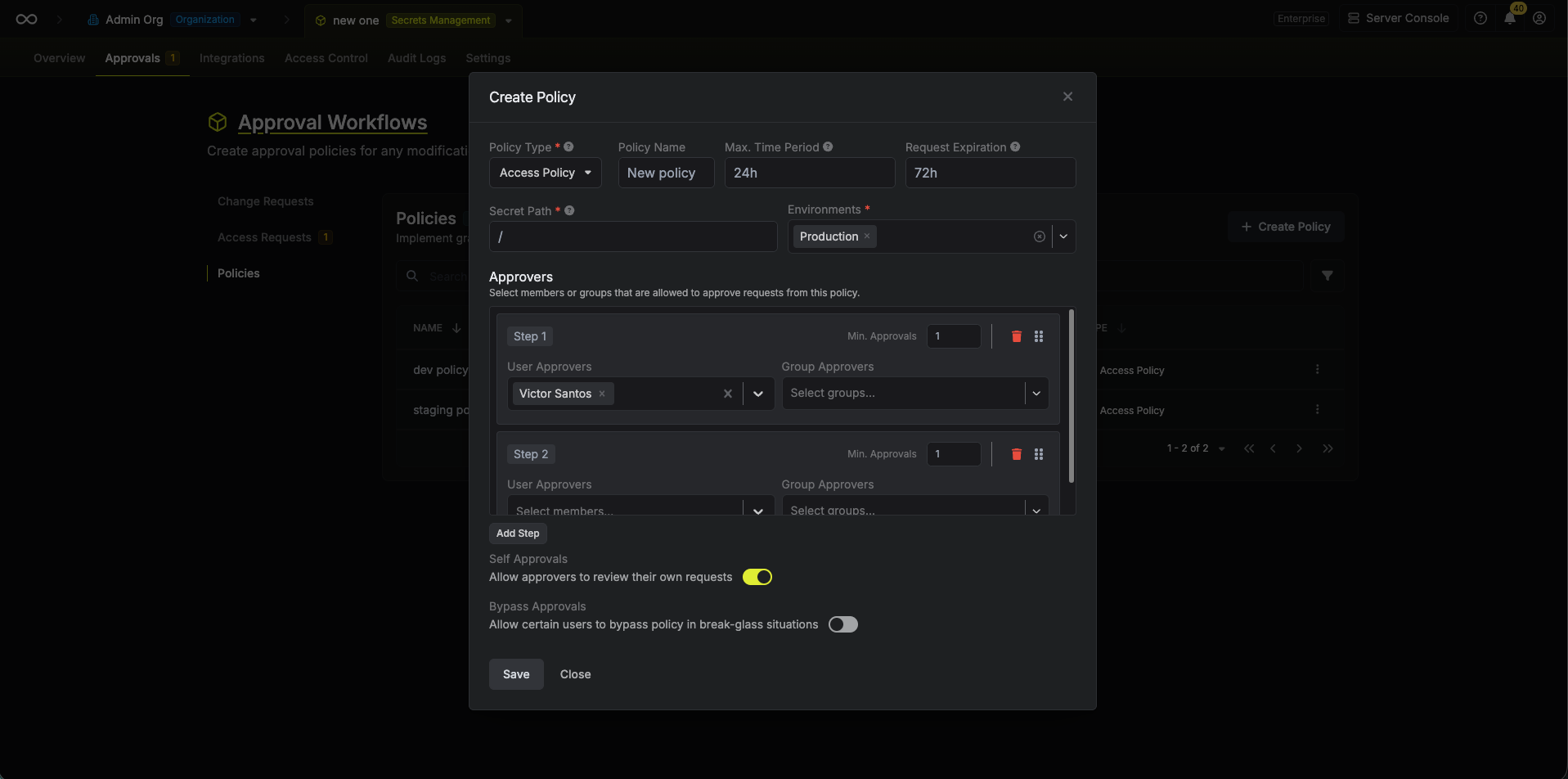 Each step can have:
Each step can have:
- User Approvers: Individual users who can approve at this step
- Group Approvers: User groups whose members can approve
- Min. Approvals Required: The minimum number of approvals needed before moving to the next step
Self-Approval Settings
The Self Approvals toggle controls whether users who are designated as approvers can approve their own access requests. Disable this option to require approval from a different approver.Break-Glass (Bypass) Settings
The Bypass Approvals option enables emergency access in break-glass situations:- When enabled (Soft Enforcement), designated users can bypass the approval workflow and grant themselves immediate access
- When disabled (Hard Enforcement), all requests must go through the full approval process
- You can specify which users or groups are allowed to bypass
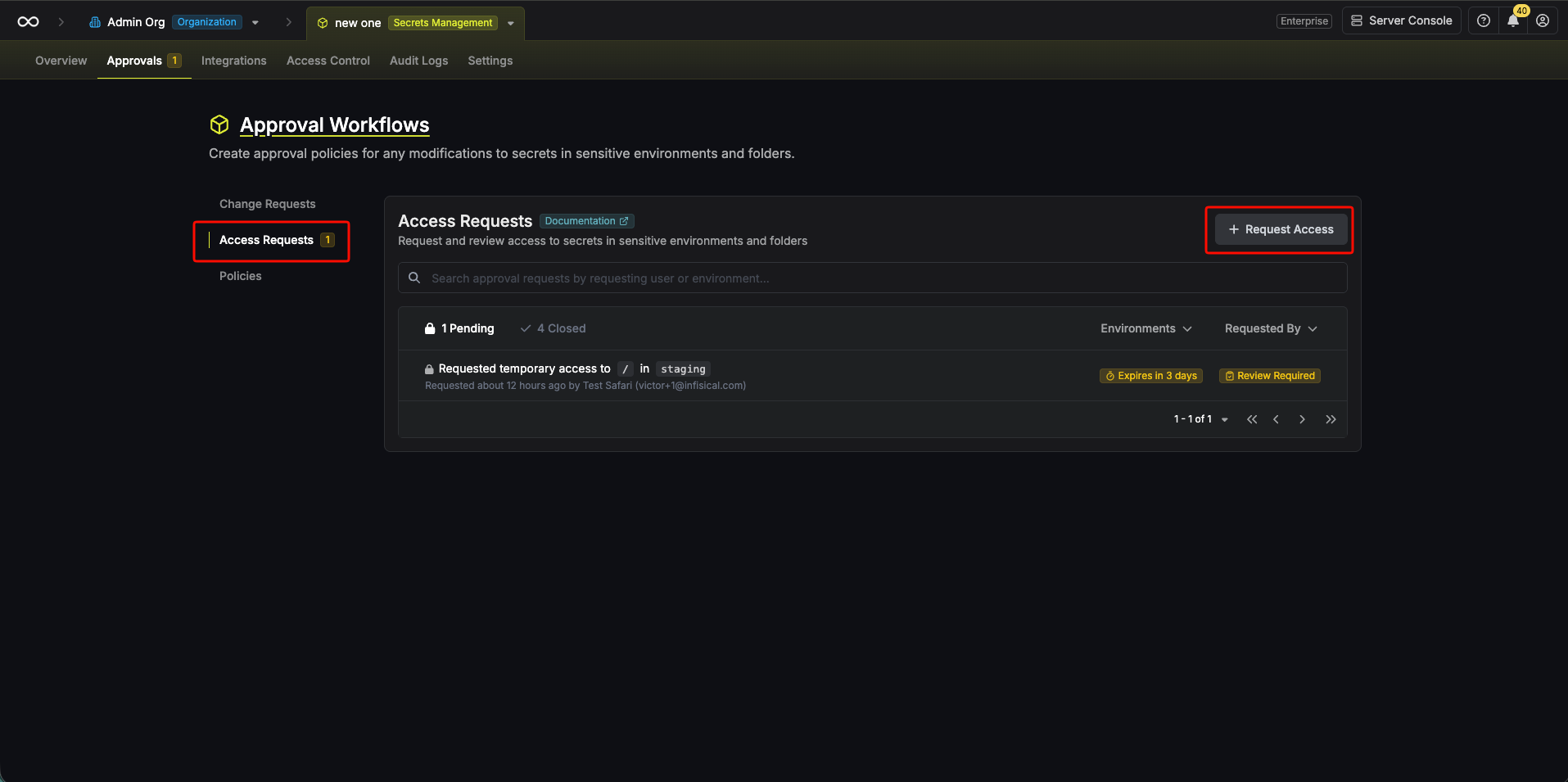
Submitting Access Requests
Once access policies are configured, users can request access to resources covered by those policies.Creating a Request
- Navigate to the Access Requests menu in the sidebar.
- Click Request Access.
- Fill in the request details:
- Environment: Select the target environment
- Secret Path: Choose the folder path
- Permissions: Select the access level (Read, Create, Edit, Delete)
- Access Duration: Choose temporary access with a specific duration or permanent access (limited by policy’s Max Time Period)
- Note: Optional justification or context for the request
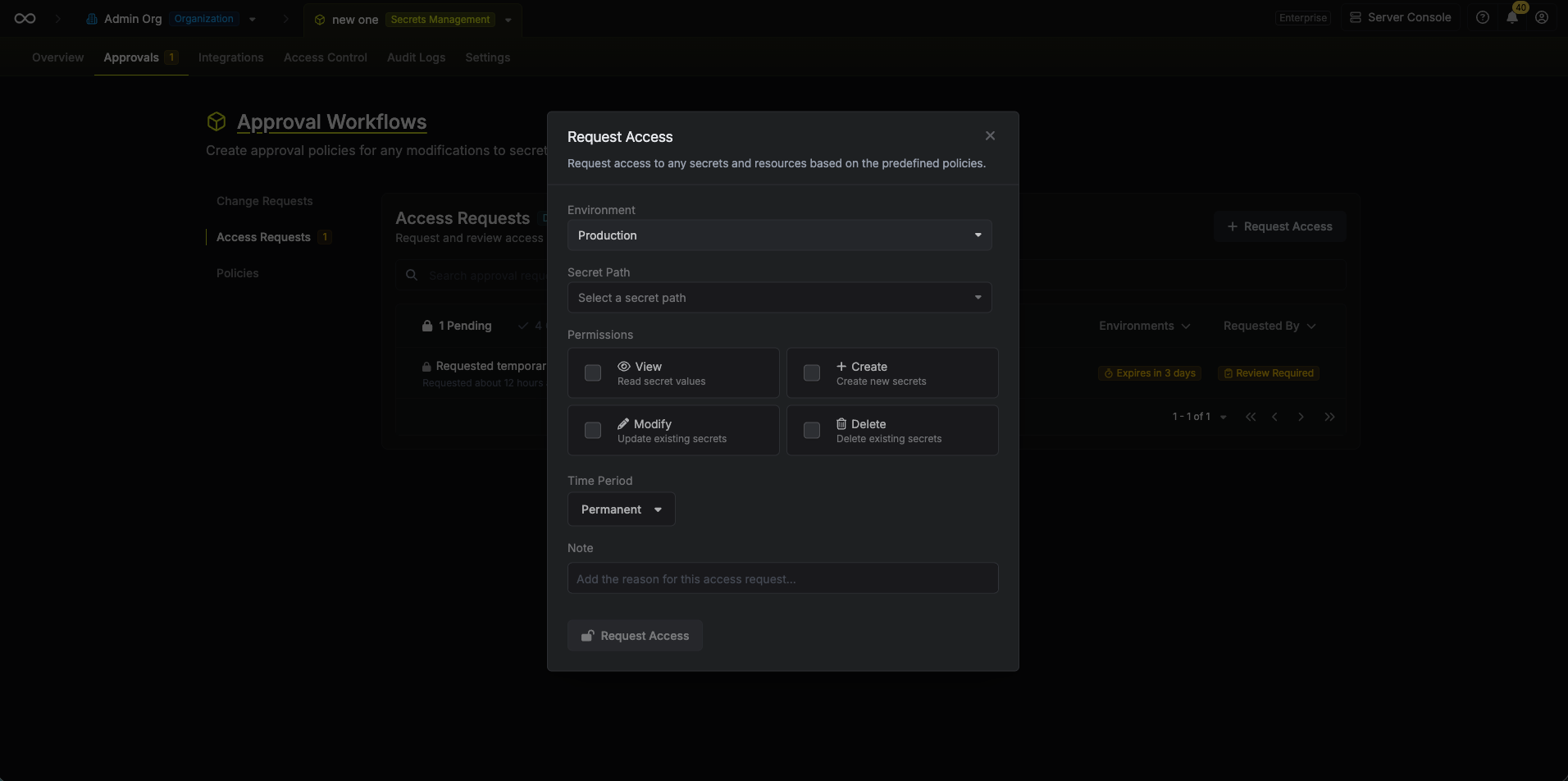
If a policy has a Max Time Period configured, the requested duration cannot exceed this limit.
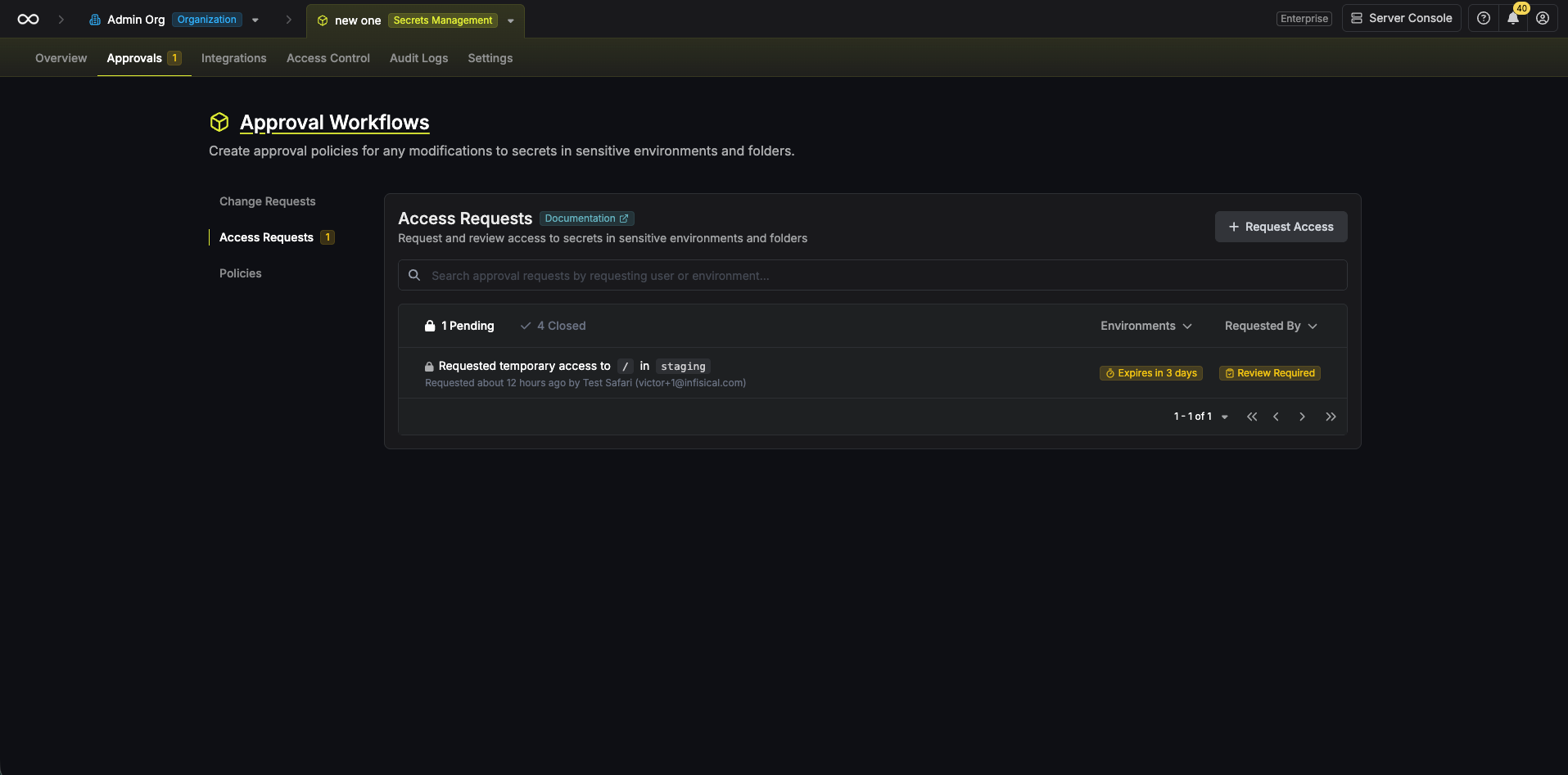
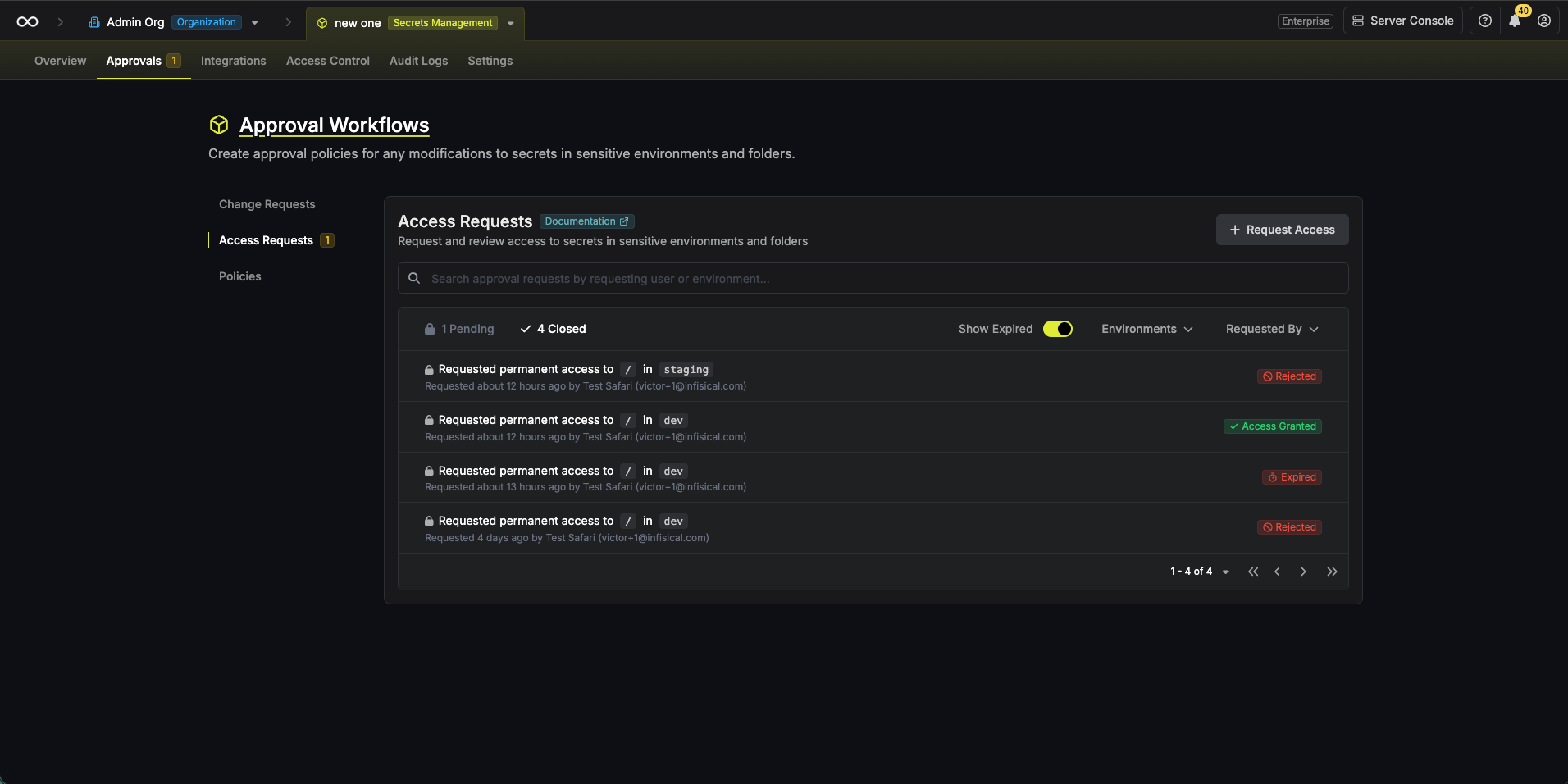
Reviewing Access Requests
Eligible approvers receive email notifications when access requests are submitted. They can review and act on requests from the dashboard.Pending vs. Closed Requests
The access requests dashboard shows two tabs:- Pending: Open requests awaiting approval (excludes expired requests)
- Closed: Finalized requests including approved, rejected, revoked, and expired requests
Reviewing a Request
Click on any request to open the review modal with full details: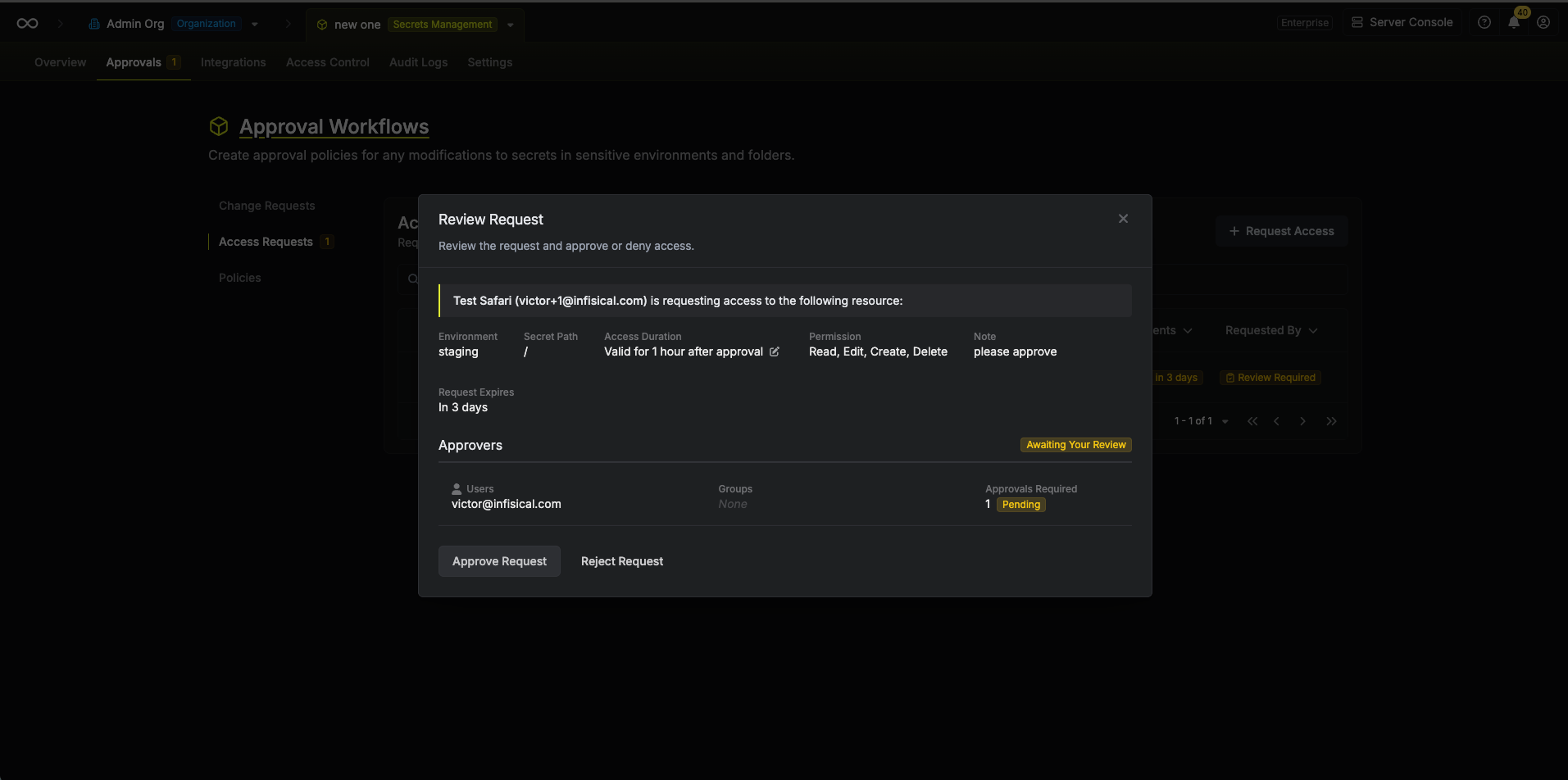
Editing Access Duration
Approvers can modify the access duration before approving a request by clicking the Edit icon next to the duration field. This allows shortening the requested timeframe when appropriate.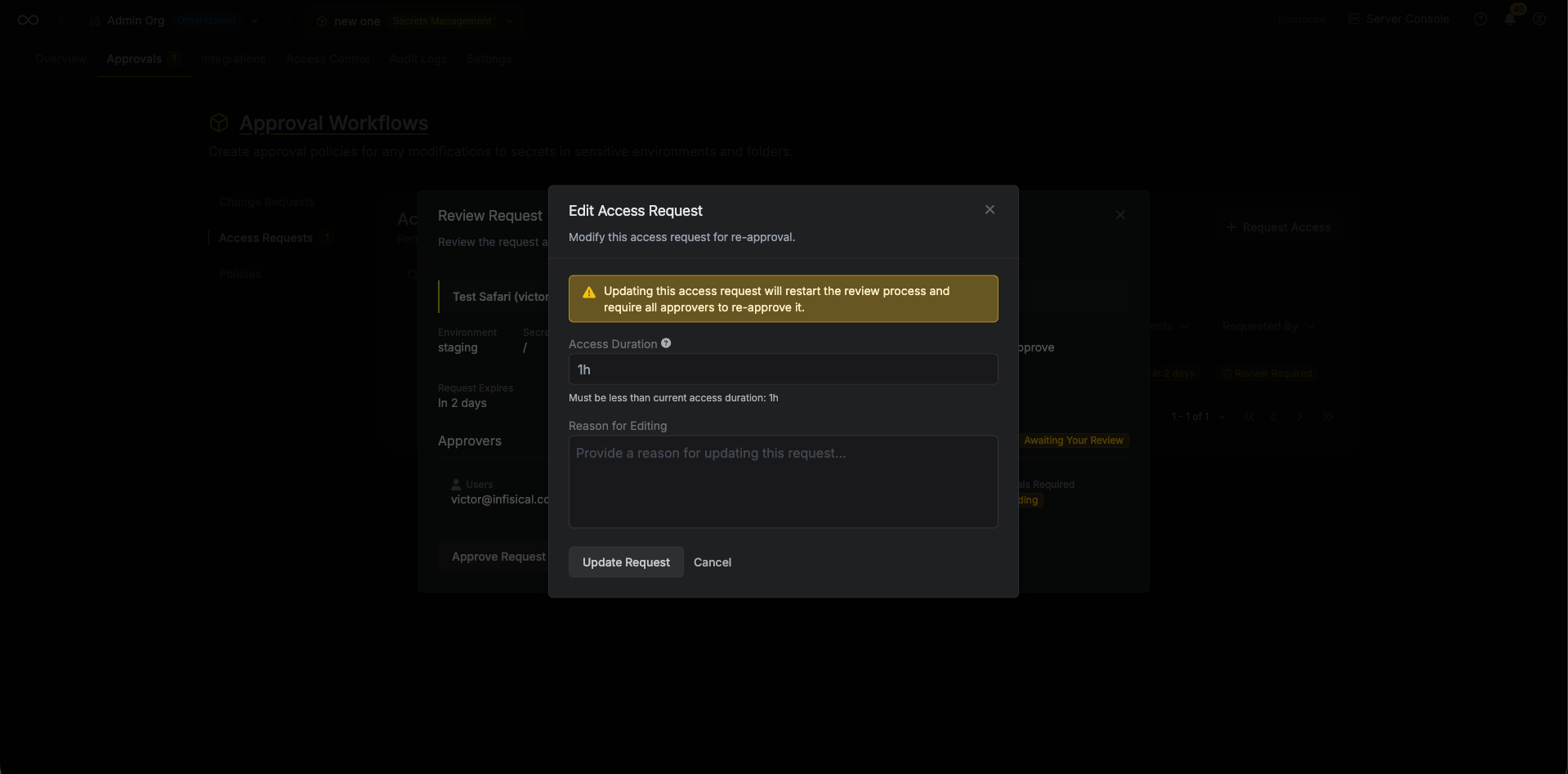
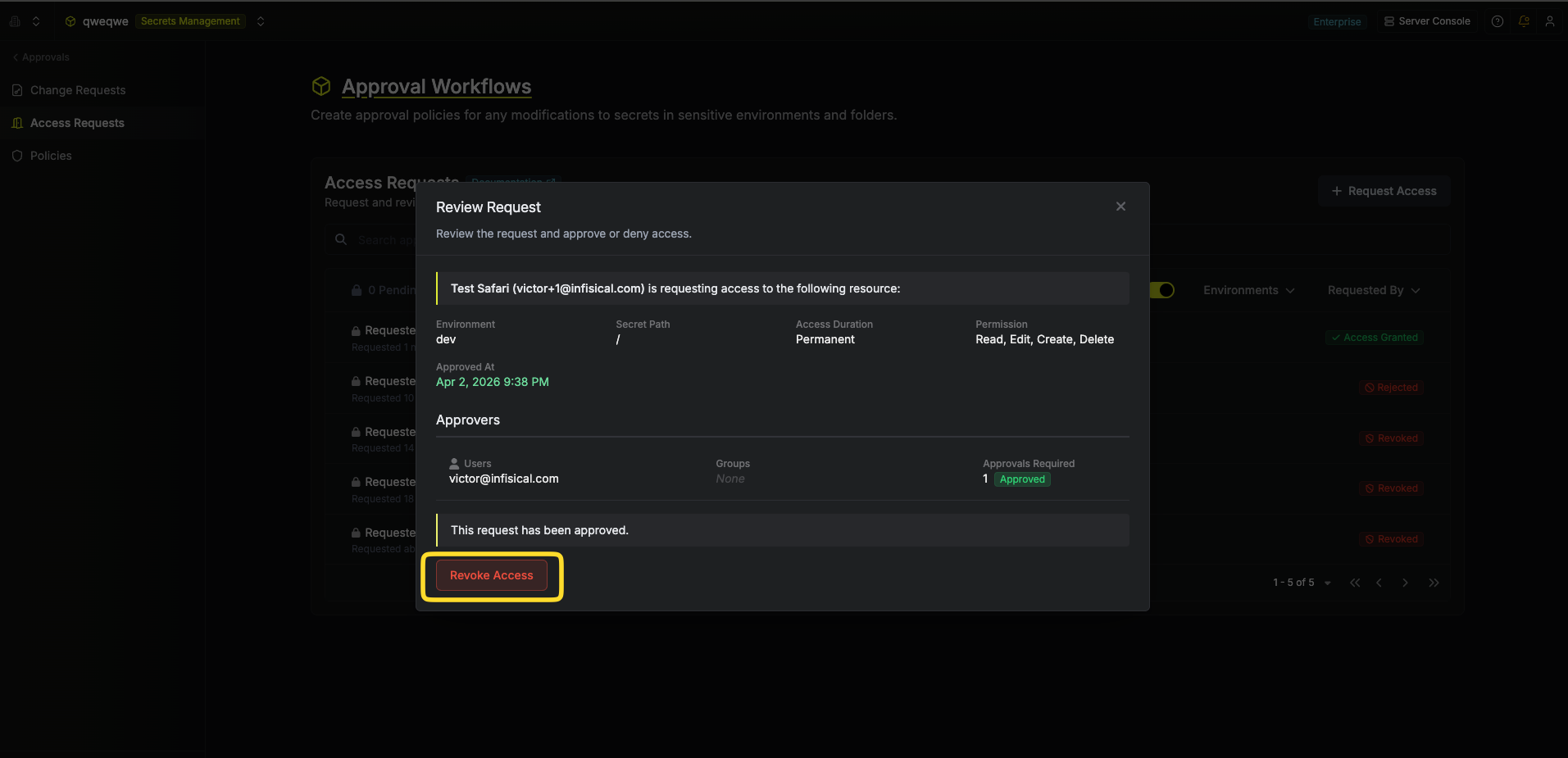
Revoking an Approved Request
Approvers can revoke a previously approved access request at any time. Revoking an access request immediately deletes the associated privilege, removing the user’s access.How to Revoke
- Navigate to the Access Requests menu in the sidebar and open the Closed tab.
- Click on an approved request to open the review modal.
- Click the Revoke Access button visible to policy approvers.
- Confirm the revocation.
Only users who are designated approvers for the access policy can revoke approved requests. Once revoked, the request moves to the Revoked status and cannot be re-approved.