Secret Validation Rules let you define constraints that secrets must satisfy before they can be created or updated. This helps teams enforce consistent naming conventions, prevent weak or malformed values, and maintain compliance standards across environments — all automatically at write time. For example, you can require that all secret keys in production followDocumentation Index
Fetch the complete documentation index at: https://infisical.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
UPPER_SNAKE_CASE, that values meet a minimum length, or that database connection strings always start with a specific prefix.
How It Works
When a secret is created or updated, Infisical checks it against all active validation rules whose scope (environment and folder path) matches the secret’s location. If any constraint is violated, the secret is rejected and an error is thrown. When a secret is rejected, the actor will see an error describing which rule and constraint was violated.Validation rules are enforced on mutations only (such as create or update events). Existing secrets that were created before a rule was added are not retroactively validated.
Constraint Types
Each rule contains one or more constraints. A constraint specifies what to check (the secret key or value) and how to check it.| Constraint | Description | Example |
|---|---|---|
| Min Length | The target must be at least N characters long | Value must be at least 8 characters |
| Max Length | The target must be at most N characters long | Key must be at most 64 characters |
| Regex Pattern | The target must match a regular expression | Key must match ^[A-Z][A-Z0-9_]*$ |
| Required Prefix | The target must start with specific text | Value must start with https:// |
| Required Suffix | The target must end with specific text | Key must end with _SECRET |
| Prevent Value Reuse | The new value must not match any of the last N versions | Value must not match the last 10 versions |
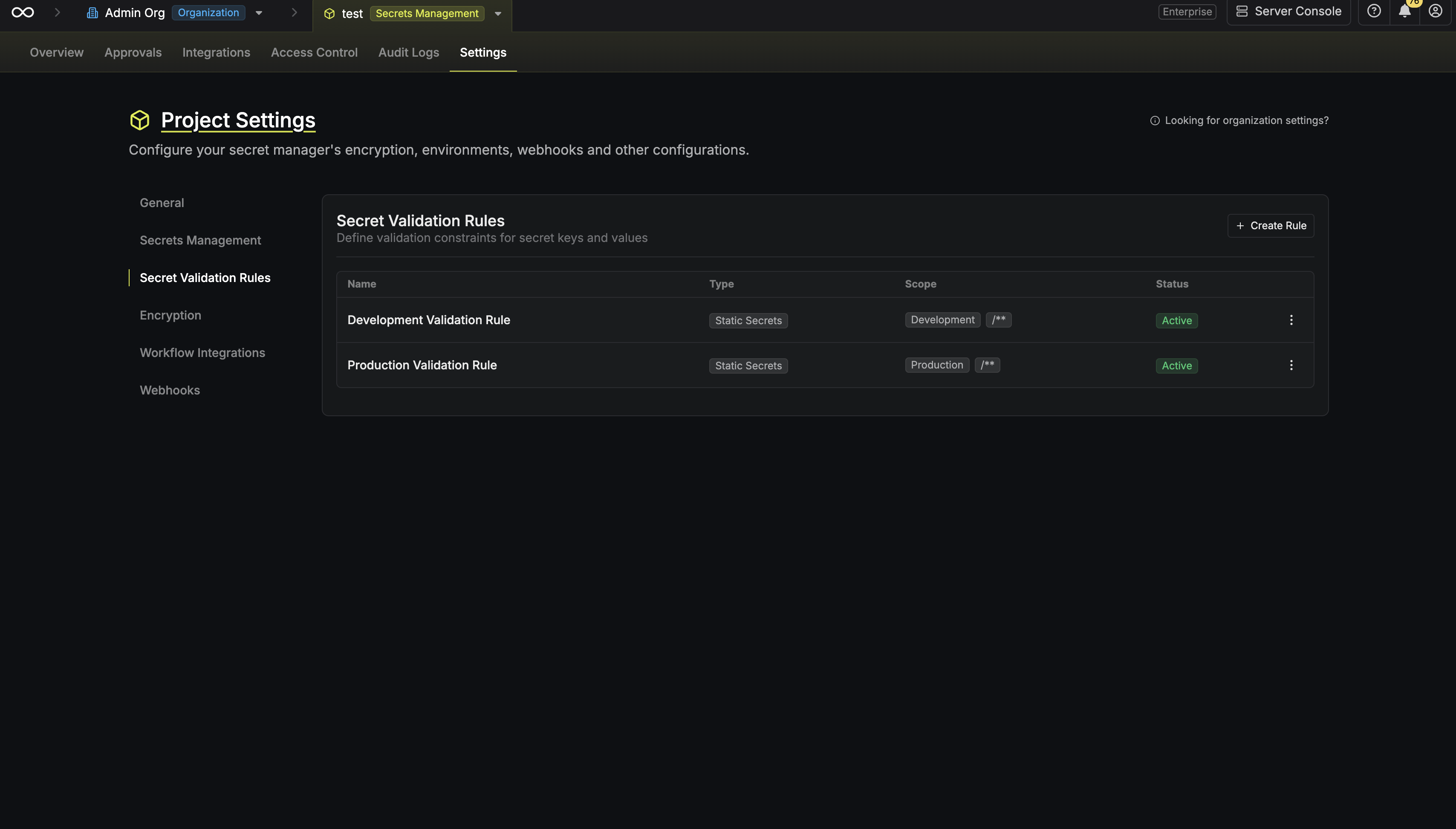
Scoping Rules
Every rule is scoped to control where it applies:- Environment: Restrict the rule to a specific environment (e.g.,
production), or apply it to all environments. - Folder Path: Restrict the rule to a specific folder path. Supports glob patterns (e.g.,
/**for all paths,/services/*for immediate subfolders of/services).
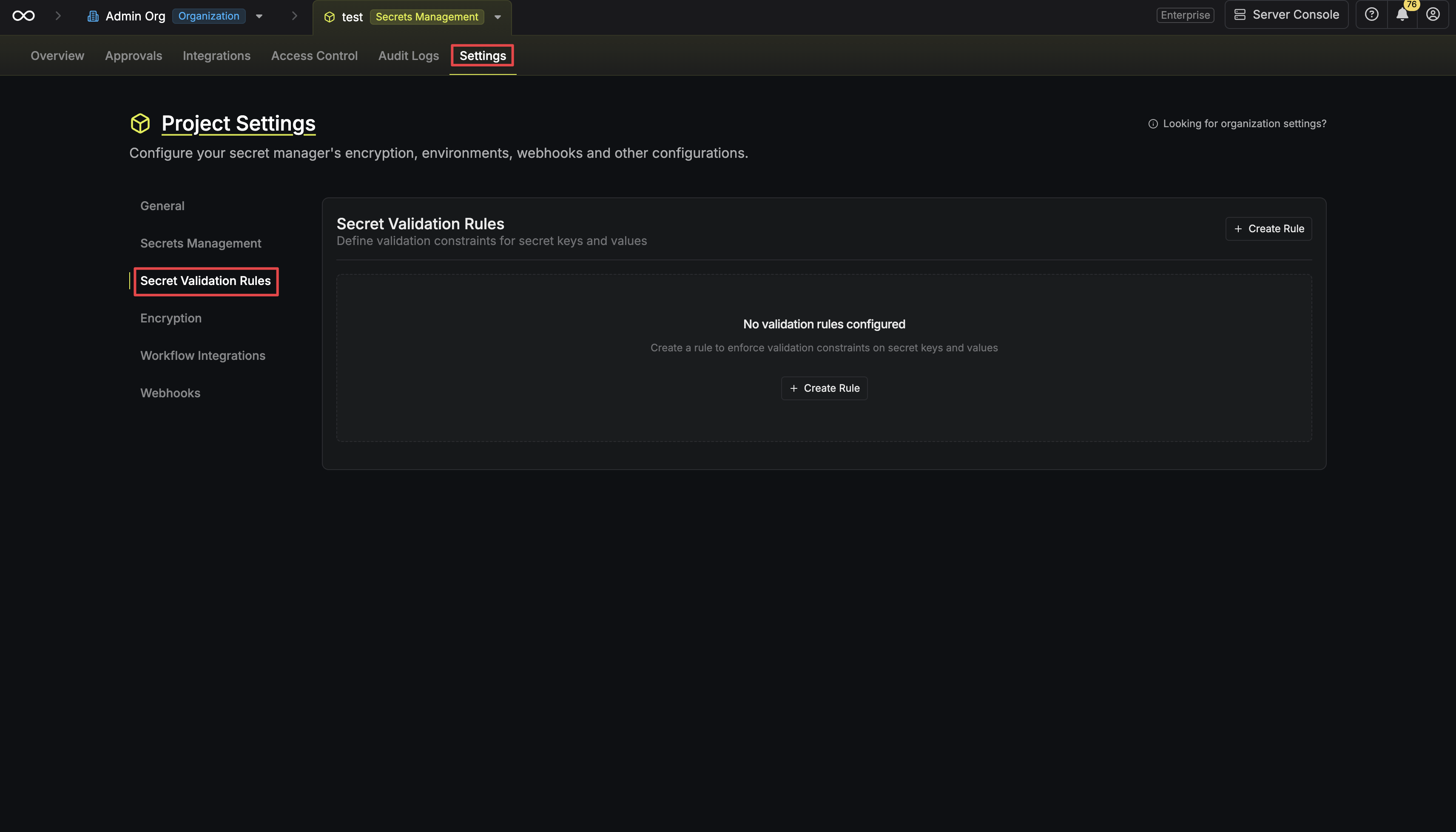
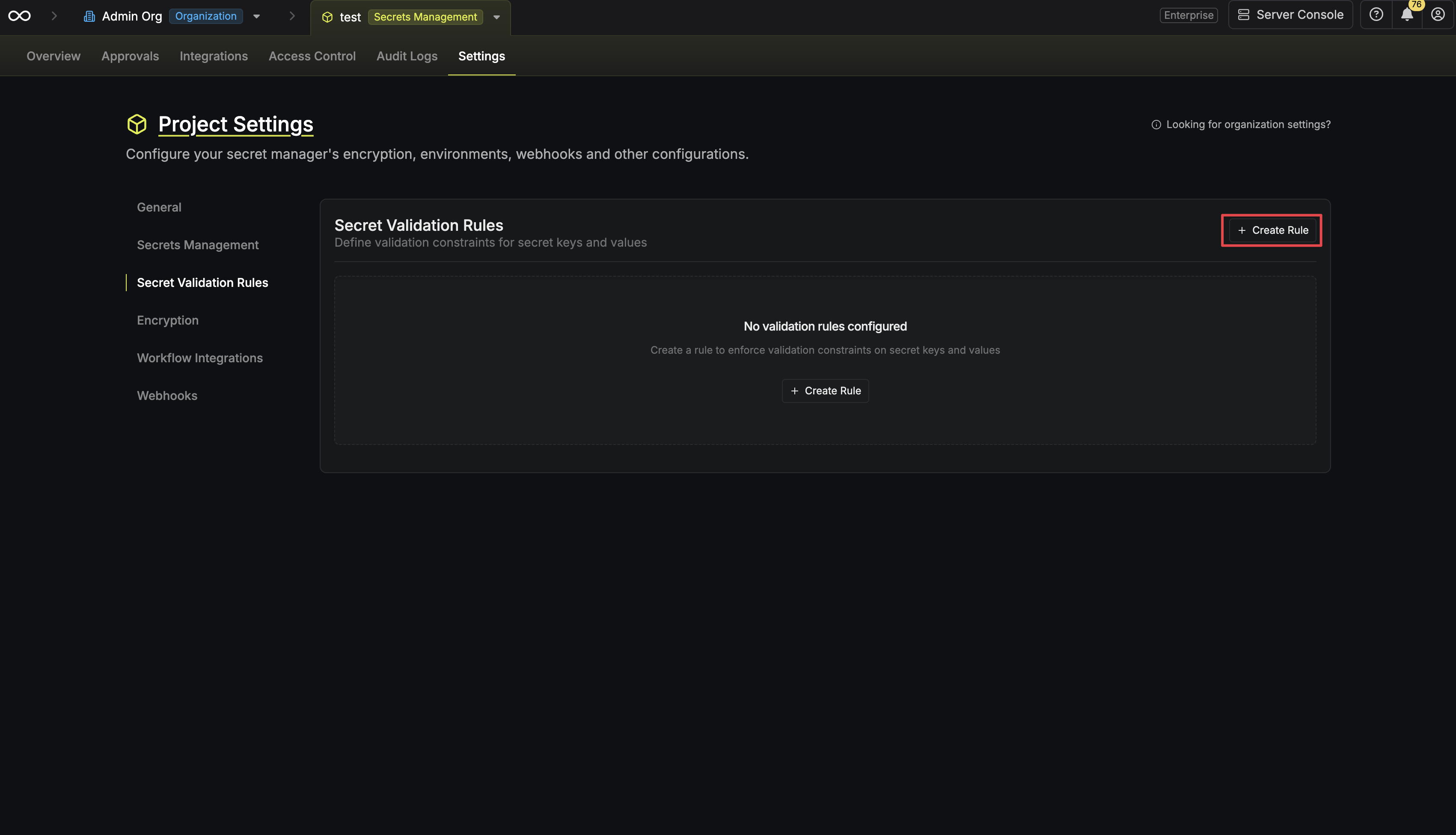
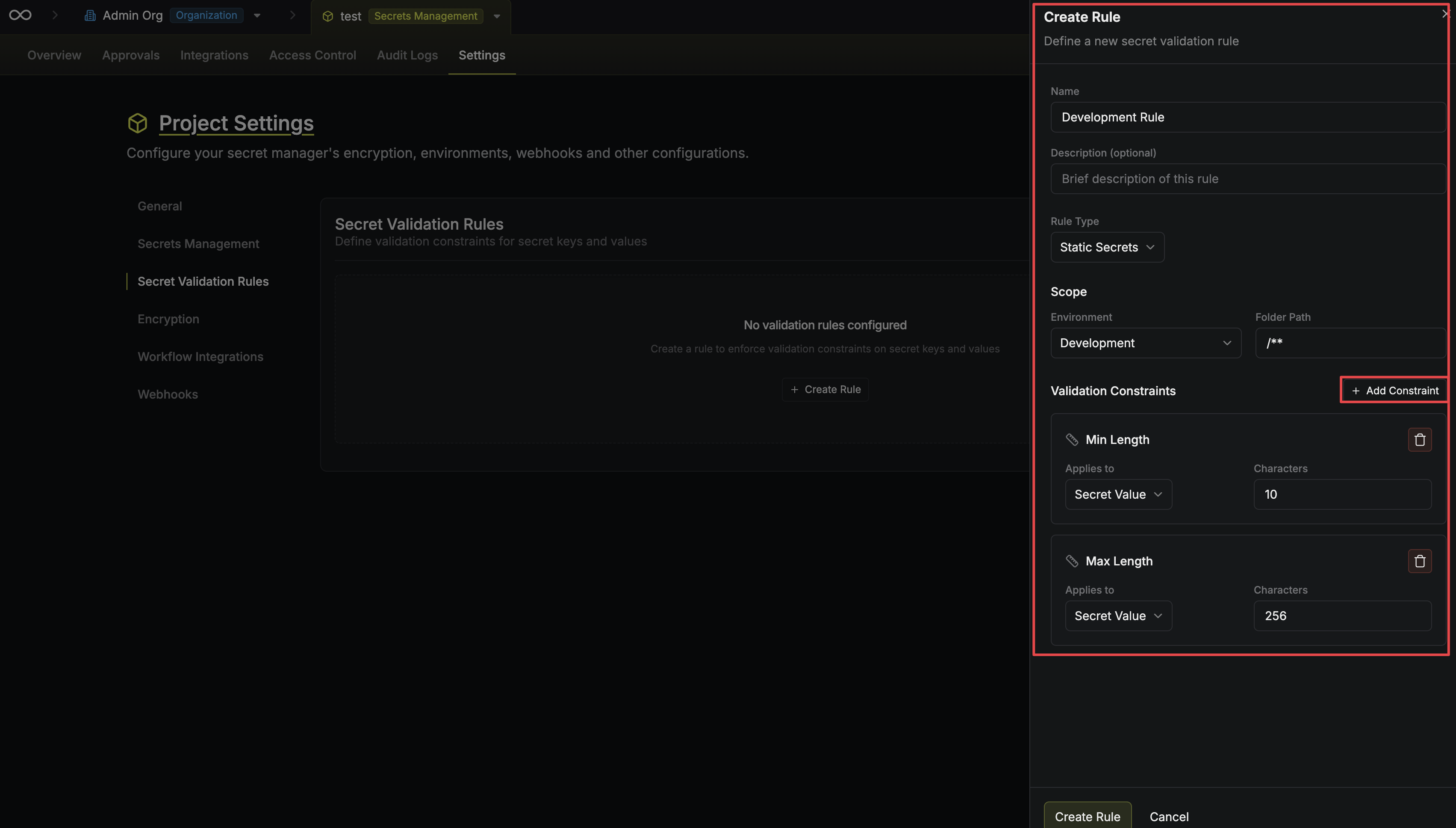
Creating a Rule
Configure the rule
Rule Details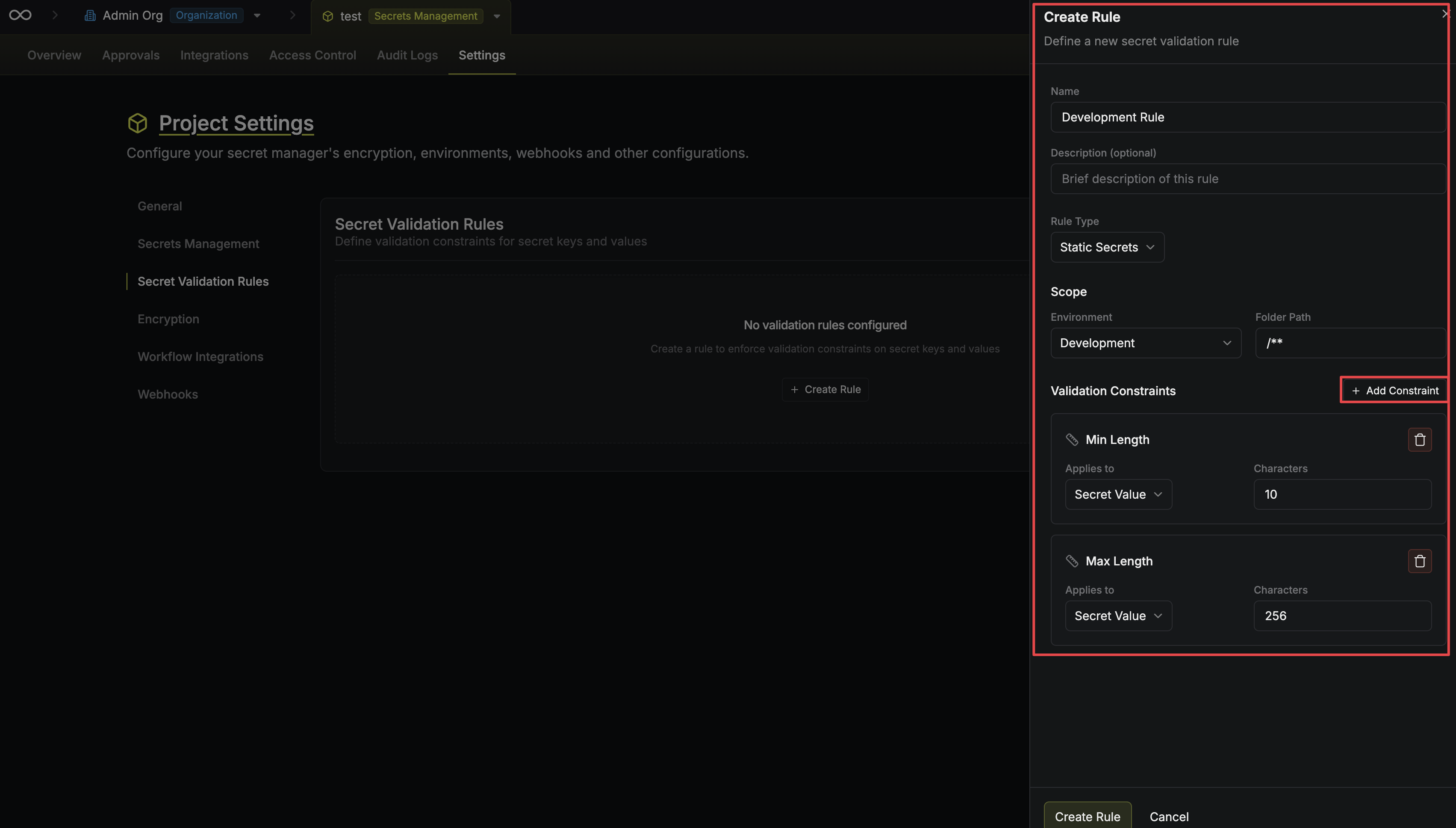
- Name — A descriptive name (e.g., “Production key naming convention”).
- Description (optional) — A brief explanation of what the rule enforces and why.
- Rule Type — Currently supports Static Secrets.
- Environment — Choose a specific environment or “All Environments”.
- Folder Path — The path scope, supporting glob patterns (e.g.,
/**).
Overlapping Rules
Infisical prevents you from creating rules that would conflict with each other. If two rules apply to the same scope (overlapping environment and folder path) and share a constraint of the same type targeting the same field (key or value), the second rule will be rejected. For example, you cannot have two separate “Regex Pattern on key” constraints in overlapping scopes, as they could contradict each other. Instead, combine the patterns into a single rule.Example Use Cases
Enforce UPPER_SNAKE_CASE naming
Enforce UPPER_SNAKE_CASE naming
Create a rule scoped to all environments with a Regex Pattern constraint on the secret key:
- Pattern:
^[A-Z][A-Z0-9_]*$
UPPER_SNAKE_CASE convention (e.g., DATABASE_URL, API_KEY), rejecting names like mySecret or api-key.Require minimum value length
Require minimum value length
Create a rule with a Min Length constraint on the secret value:
- Minimum:
8
Enforce URL format for connection strings
Enforce URL format for connection strings
Create a rule scoped to a specific folder path (e.g.,
/database/*) with a Required Prefix constraint on the secret value:- Prefix:
postgresql://
Enforce environment-specific key suffixes
Enforce environment-specific key suffixes
Create a rule scoped to the
production environment with a Required Suffix constraint on the secret key:- Suffix:
_PROD
Prevent reuse of old secret values
Prevent reuse of old secret values
Create a rule with a Prevent Value Reuse constraint on the secret value:
- Previous versions:
10