

Infisical vs Doppler
Companies choose Infisical over Doppler to satisfy their compliance, security, and scalability needs.
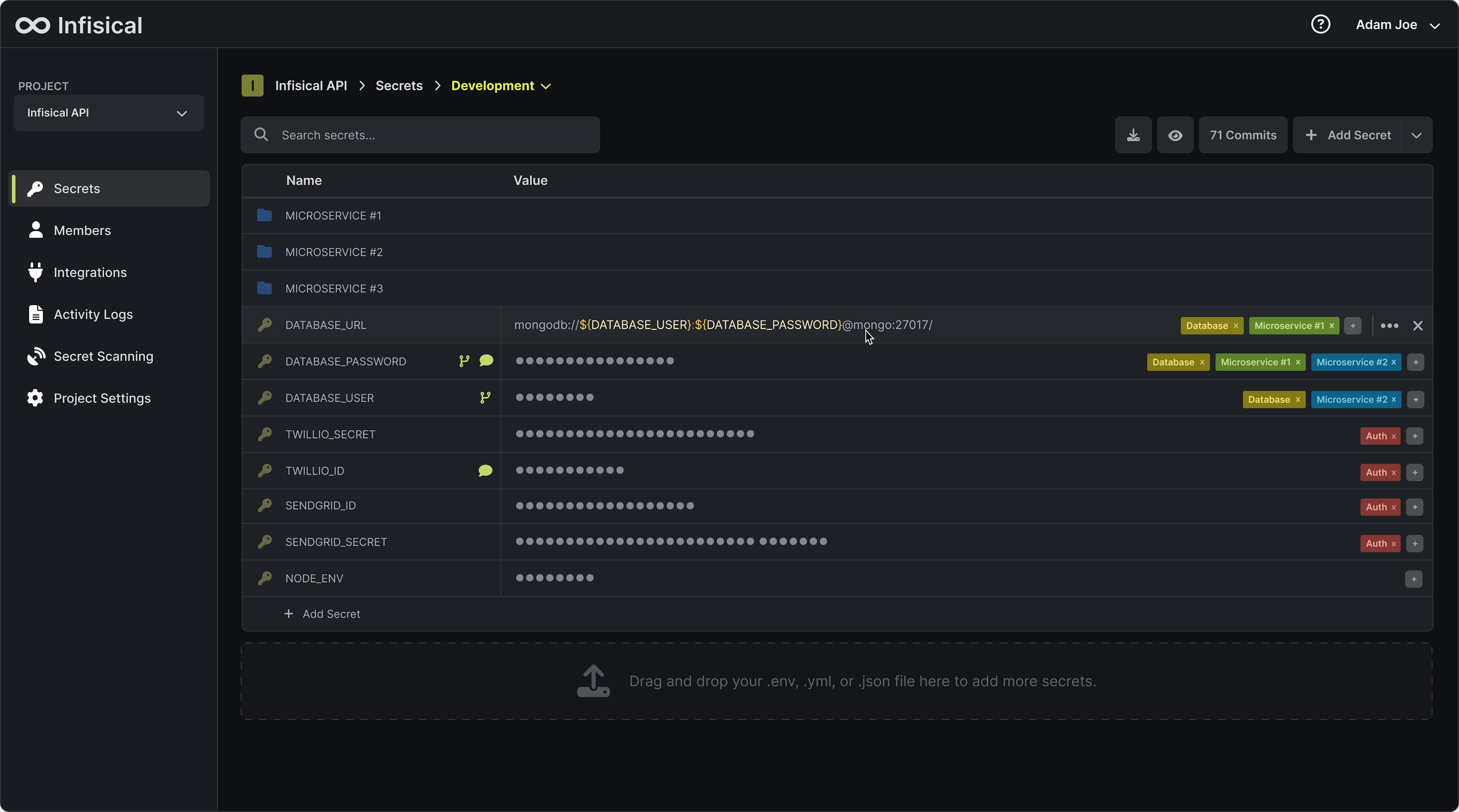
Meet the contenders Meet Infisical Infisical is the all-in-one secrets management platform built to help developers manage application secrets, certificates, SSH keys, and configurations across modern infrastructure — providing capabilities for automatic secret rotation, leak prevention, and approval workflows.
Meet Infisical Infisical is the all-in-one secrets management platform built to help developers manage application secrets, certificates, SSH keys, and configurations across modern infrastructure — providing capabilities for automatic secret rotation, leak prevention, and approval workflows. Meet DopplerDoppler is a closed-source tool designed to manage and secure application secrets in modern computing environments. It provides a list of integrations that help sync secrets across application infrastructure.
Meet DopplerDoppler is a closed-source tool designed to manage and secure application secrets in modern computing environments. It provides a list of integrations that help sync secrets across application infrastructure.
Infisical vs Doppler: The Short Version

Infisical vs Doppler: The Long Version
Infisical is suitable for you if:
You need a single source of truth to manage secrets across your engineering team and infrastructure (incl. local development, CI/CD, and production).
You care about developer experience including dev onboarding and time-to-production processes.
You want the solution to be open source to satisfy compliance requirements and/or minimize vendor lock-in.
You want to approach secret management from the `security shift left` perspective.

Doppler is suitable for you if:
Your current and future compliance requirements do not include self-hosting ability as well as end-to-end encryption.
You secret structure is 1 level deep, and you do not expect to have more complicated secret structures.
Doppler
Why does it matter?
OFFERS
PARTIALLY OFFERS
DOES NOT OFFER
Architecture & Security
Open Source
Yes, Infisical is an open source product with a community consisting of thousands of developers – link to GitHub repo.
No.
Using open source security products is considered to be the best practice. Open codebases are reviewed by thousands of security practitioners for any kinds of vulnerabilities – something that is not possible when a product is close source. In addition, it gives you direct overview of and input into the product's roadmap.
Hosting Options
Offers a hosted cloud product – signup here.
Self-hostable on your own infrastructure – instructions here.
Offers a hosted cloud product.
Not self-hostable on your own infrastructure.
Infisical can be self-hosted on any cloud or on your own infrastructure – significantly minimizing vendor lock-in and improving your company's compliance posture. Having the option of using a Cloud-hosted product is also very important if your team doesn't have the capacity to think about hosting a product themselves.
Encrypted Secrets Storage
Infisical uses TLS for encryption in transit as well as AES256-GCM for symmetric encryption and x25519-xsalsa20-poly1305 for asymmetric encryption operations – security brief here.
Doppler uses a security barrier which automatically encrypts all data leaving Doppler using a 256-bit Advanced Encryption Standard (AES) cipher in the Galois Counter Mode (GCM) with 96-bit nonces.
Encrypted Storage is important to make sure that your data stays safe and compliant.
Zero-knowledge Architecture
Infisical uses secure remote password (SRP) to handle authentication and public-key cryptography for secret sharing and syncing; secrets are symmetrically encrypted by keys decryptable only by members of the project – security brief here.
Not available. There is an alternative offering of "enterprise key management" which is a feature on Doppler's enterprise plan (not available by default).
Zero-knowdlge architecture ensures that only users themselves are able to decrypt their data – NOT Infisical (or any of Infisical's employees).
IP-allowlisting
Available – docs here.
Available under the name "Trusted IPs".
IP-allowlisting allows you to restrict which IP-addresses are able to perform operations with your secrets or any other high-importance operations (e.g., modify user permissions).
Developer Experience
Project & Environment Separation
Out of the box, Infisical allows you to structure your secrets into projects (they often correspond to git repositories) and environments (e.g., dev, staging, prod) – read more.
With Doppler, users are able to easily split secrets into projects and environments. Doppler also has a concept of configs which allows you to create variations of environments.
Proper structure allows developers to navigate and find right secrets easier and quicker.
Environment Comparison
Infisical lets developers immediately see the differences in secrets across various environments via a web dashboard overview.
In Doppler, users don't have a simple environment overview screen. Users are only able to see if a certain environment is missing a secret compared to the other ones.
Being able to easily see this, allows developers to spot bugs in seconds as well as makes programs more reliable.
Secret Referencing
Infisical lets developers reference secrets within the projects across different folders and environments.
Doppler lets developers reference secrets across projects and environments.
Secret referencing helps establish the single source of truth and minimize bugs related to updating values in different places.
Personal Secret Overrides
Developers can override secrets for themselves while keeping the values unchanged for rest of the team/infrastructure – docs here.
Not available.
This is useful for local development in order to not disrupt the workflow of your teammates as well as for compliance purposes (e.g., Database Access Tokens should be unique for every developer)
Deeper Secret Structures
Infisical lets you form secrets into directories from which you are then able to organize them into any structure you want.
Doppler only allows to have a list of secrets without being able to create more advanced structures.
As your product/project grows, this will be very important to allow for scaling (e.g., you can have secerts for each microservice in different folders).
Secret Versioning
Yes, granular secret versioning with timestamps.
Yes, fairly identical secret versioning structure to what Infisical offers.
It is useful to know how the value of a certain secret has been changing over time for debugging and compliance purposes.
Point-in-time Recovery
Yes, you can roll back secrets in any projects to any snapshot. It works in a way comparable to git commits.
Available.
Whenever someone makes a mistake in adding/editing/deleting a secret (or one simply needs to rollback a deployment), this becomes very handy.
Ways to access secrets
Command Line Interface
Infisical offers a fully language- and platform-agnostic CLI. It allows to automatically inject application secrets as environment variables, modify secrets, and more – docs here.
Doppler provides a similar platform- and language-agnostic CLI.
This way tends to be the easiest to get set up with secrets management. It also enables fully synchronized local development – also in larger teams.
SDKs
Infisical currently offers SDKs for Python, NodeJS, Go, Java, and more – see documentation.
Doppler offers SDKs for Python and NodeJS, but not other languages.
SDKs tend to be a more reliable way of accessing secrets even though they require more work – which often makes it a preferred choice for larger and more developed teams.
Third-party Integrations
Infisical lets you push secrets to various 3rd-party services (e.g., Vercel, Github Actions, Circle CI) – ultimately becoming a true single source of truth for you secrets. You can find the docs here.
Doppler provides a wide range of integrations. Keep in mind that these integrations are subject to corresponding pricing limits.
Automatic 3-rd party integrations create a single source of truth for your secrets in Infisical. From there, with just a couple clicks, you can distribute across other infrastructure services that your company is using.
API
Universal API that lets you perform a range of secret operations – docs here.
Universal API with fairly deep capabilities of secret operations.
API gives you maximum flexibility with what you want to do with your application secrets – even though it is the right choice for only very few teams.
Kubernetes Operator
Infisical's Operator provides multiple CRDs to sync secrets bidirectionally, manage dynamic secrets, and handle automatic lease management – read documentation.
Available.
Teams running Kubernetes often struggle with keeping secrets in sync between their secret manager and their clusters. The operator solves this by automating the synchronization both ways and managing secret lifecycles, saving DevOps teams hours of manual work.
Kubernetes CSI Provider
Infisical offers CSI provider support for direct pod mounting of secrets, with service account authentication and auto-syncing capabilities – read documentation.
Not available.
Direct pod injection eliminates the need to store secrets as Kubernetes resources, reducing exposure and attack surface. Combined with service account authentication, this creates a more secure and maintainable secret delivery pipeline.
Agent
Available – read documentation.
Not available.
Agent-based approach eliminates the need to modify application logic by enabling clients to decide how they want their secrets rendered through the use of templates.
Native Authentication Methods
Not available.
Native Authentication Methods allow organization to solve secret zero problem and go fully multi-cloud.
Compliance
Audit Logs
Available – docs here.
Available.
Activity/audit logs let you establish the highest level of compliance across you organization. They're especially important in the secret management domain given how sensitive application secrets are.
Access Controls
Infisical offers both role-based and attribute-based access controls. You can specify if developers are able to access certain secrets, edit them, or only add the new ones to a particular environment. You are also able to create custom roles – docs here.
Available, but in a fairly restrictive manner.
Access controls are paramount for ensuring compliance and security as your organization starts growing. They are also incredibly useful for preventing accidental errors in adding/editing/deleting secrets.
Access Requests & Temporary Access
Infisical provides a powerful temporary access system that automatically revokes access after a set duration. Also supports access requests for long-term needs.
Not available.
Development teams often face a dilemma: wait for lengthy approval processes or compromise security with permanent access grants. Temporary access solves this - no more forgotten permissions or compliance headaches.
Approval Workflows
Infisical lets organization set up secret change policies for highly sensitive environments – read documentation.
Not available, but similar functionality exists on the enterprise tier.
Approval workflows ensure the highest levels of compliance and reliability when performing secret changes. Similar to git PRs, every change of secrets in sensitive environments will have to be reviewed based on the predefined policies.
Secret Rotation
Available. Allows for both automatic rotation and dynamic secrets generation – docs here.
Available, but mostly requires upgrading to the enterprise tier.
Secret rotation allows your team save a lot of time and reduce risks of rotating secrets manually. Secret rotation becomes fully automated which dramatically improves your security posture.
Other
Key Management Service (KMS)
Infisical offers built-in KMS functionality for managing cryptographic keys with support for HSM integration – read documentation.
Not available.
Centralizing encryption keys reduces security risks, enables automated rotation, and simplifies compliance tracking. Essential for teams handling sensitive data or meeting security standards.
Certificate Lifecycle Management (PKI)
Infisical can be used to create a Private Certificate Authority (CA) hierarchy, issue X.509 certificates for internal use, and more - read documentation.
Not available.
In order to fight secret sprawl and fully centralize secrets management, it is important for a secrets management solution to manage certificate lifecycle.
Secret Sharing
Infisical offers secure, zero-knowledge secret sharing with time and view count limits. Available in-app or without signup at share.infisical.com.
Not available.
Developers frequently need to share secrets with team members, contractors, or other third parties, which can be risky due to potential leaks or misuse. Infisical offers a secure solution for sharing secrets over the internet.
SSH Access Management
Infisical lets you generate and manage short-lived SSH credentials through customizable certificate templates – read documentation.
Not available.
SSH key management traditionally leads to security risks from permanent, untracked keys scattered across servers. Using short-lived certificates instead of static keys eliminates these risks and provides clear audit trails of who accessed what and when
Starting with Infisical is simple, fast, and free.

USE CASES
DEVELOPERS
CONTACT