Centralized secrets management is becoming more and more important. API keys, auth tokens and other credentials are constantly being ingested (and sometimes committed) by LLMs. Supply chain attacks are on the rise. And .env files are no longer enough to cope with it all.
Not managing secrets well leads to a problem called secret sprawl, which could lead to data breaches, leaks of sensitive credentials, and low developer efficiency.
Depending on the use case, there are a number of options to choose from:
-
Cross-cloud secrets management solutions
-
Cloud-specific secrets managers
-
Open source secret management projects
-
In-house built secret management solutions
If you’re exploring secrets management solutions, you’ll find the advantages and drawbacks of each approach as well as popular tools within each category.
How do secrets managers compare?
| Tool | License | Self-host | Managed cloud | Multi-cloud | Scope beyond secrets | Best for |
|---|---|---|---|---|---|---|
| Infisical | MIT (open source) | Yes | Yes | Yes | PKI, PAM, secrets scanning, AI agent security | Teams that want an all-in-one identity security platform with a developer-first UX |
| HashiCorp Vault | BSL (source-available) | Yes | Yes (HCP) | Yes | Encryption, PKI | Large enterprises with dedicated platform engineering teams |
| OpenBao | MPL 2.0 (open source) | Yes | No | Yes | Encryption, PKI | Teams that want Vault’s architecture without BSL or IBM |
| Doppler | Proprietary | No | Yes | Yes | N/A | Small to mid-sized teams comfortable with a cloud-only managed service |
| AWS Secrets Manager | Proprietary | No | Yes | No (AWS only) | N/A | Stacks that live entirely on AWS |
| GCP Secret Manager | Proprietary | No | Yes | No (GCP only) | N/A | Stacks that live entirely on GCP |
| Azure Key Vault | Proprietary | No | Yes | No (Azure only) | Keys, certificates | Stacks that live entirely on Azure |
| SOPS | MPL 2.0 (CNCF) | N/A (CLI tool) | No | Yes (KMS-agnostic) | N/A | GitOps workflows and lightweight file-based encryption |
Cross-cloud secrets managers
Unlike provider-specific offerings like AWS Secrets Manager, cross-platform secrets management software is not tied to any specific cloud. It can be self-hosted on any infrastructure, or used as a managed service.
Among cross-cloud providers, Infisical is open-source, which enables it to be hosted on any infrastructure. HashiCorp’s Vault operates under a lesser-known “Business Source” license, which makes the source code available to customers. Doppler is not open-source which means it can only be used as a managed service.
Let’s compare the options:
1. Infisical
Infisical is an open-source identity security platform. Most teams adopt Infisical for best-in-class secrets management, including a dedicated vault for AI agents, but it also features certificate management (PKI), privileged access management (PAM), secrets scanning, and more.
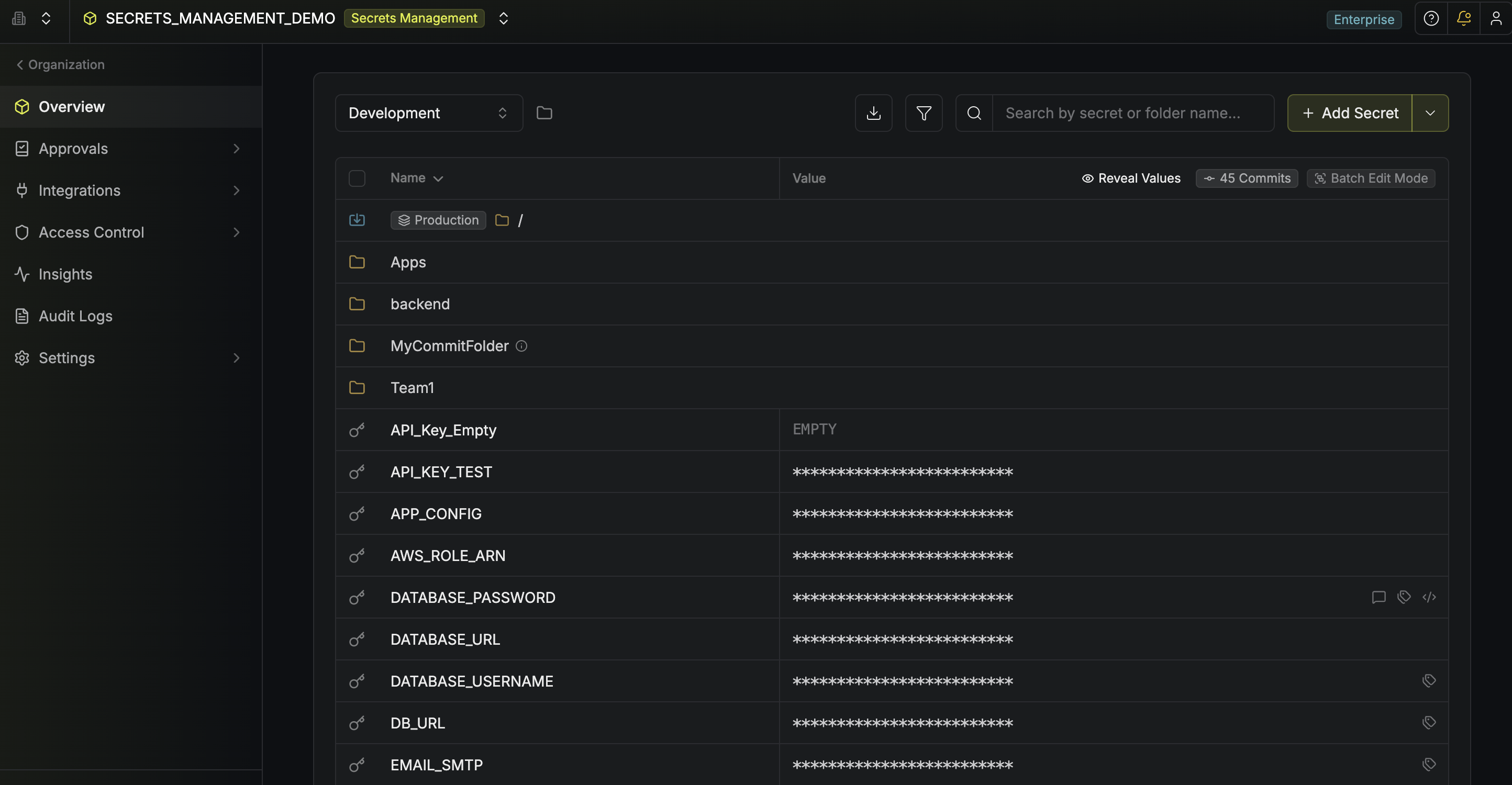
Infisical provides an end-to-end set of tools that cover all aspects of secrets management: from secure version-controlled secret storage, to secret rotation, to integrations across infrastructure, to secret scanning and leak prevention.
Some of the main Infisical features include:
-
A unified dashboard for developers to access and modify secrets based on their permissions, with granular roles and audit logs.
-
Automatic integrations across infrastructure (Docker, Kubernetes, Terraform) and third-party services (GitHub Actions, Vercel, CircleCI).
-
Secret workflows for developer on and off-boarding, approval flows and compliant changes across environments.
-
Automated secret rotations in case of breaches or potential vulnerabilities.
-
An Infisical CLI to inject secrets as environment variables, plus SDKs and APIs for additional access patterns.
-
Continuous secret scanning and monitoring and leak prevention to git.
Pros:
-
Infisical provides an end-to-end secrets management platform across the full lifecycle, combining with certificate management, PAM, scanning and AI agent security.
-
Infisical has granular access controls, audit logs, and compliance policies without custom YAML pipelines or GitOps.
-
Automatic integrations and secret referencing functionalities help establish a single source of truth for application secrets and fight secret sprawl.
-
Infisical is open source under the MIT license, which means organizations can self-host it on their own infrastructure or use the managed cloud product for teams that don’t want the overhead of running software themselves.
-
Simple architecture: Infisical is built on Postgres and Redis. No proprietary Raft cluster to operate, no certification required to manage it.
Cons:
- Some newer products (PAM, AI agent security) are earlier in their maturity curve than secrets management, though it’s developing quickly.
Watch a video to see Infisical secrets management in action.
2. HashiCorp Vault
Vault was one of the first secret management solutions and its provider HashiCorp (HCP) was acquired by IBM in 2025. It is a thorough tool for securely storing and accessing secrets and other sensitive data (e.g., access tokens, API keys, encryption keys, password, certificates).
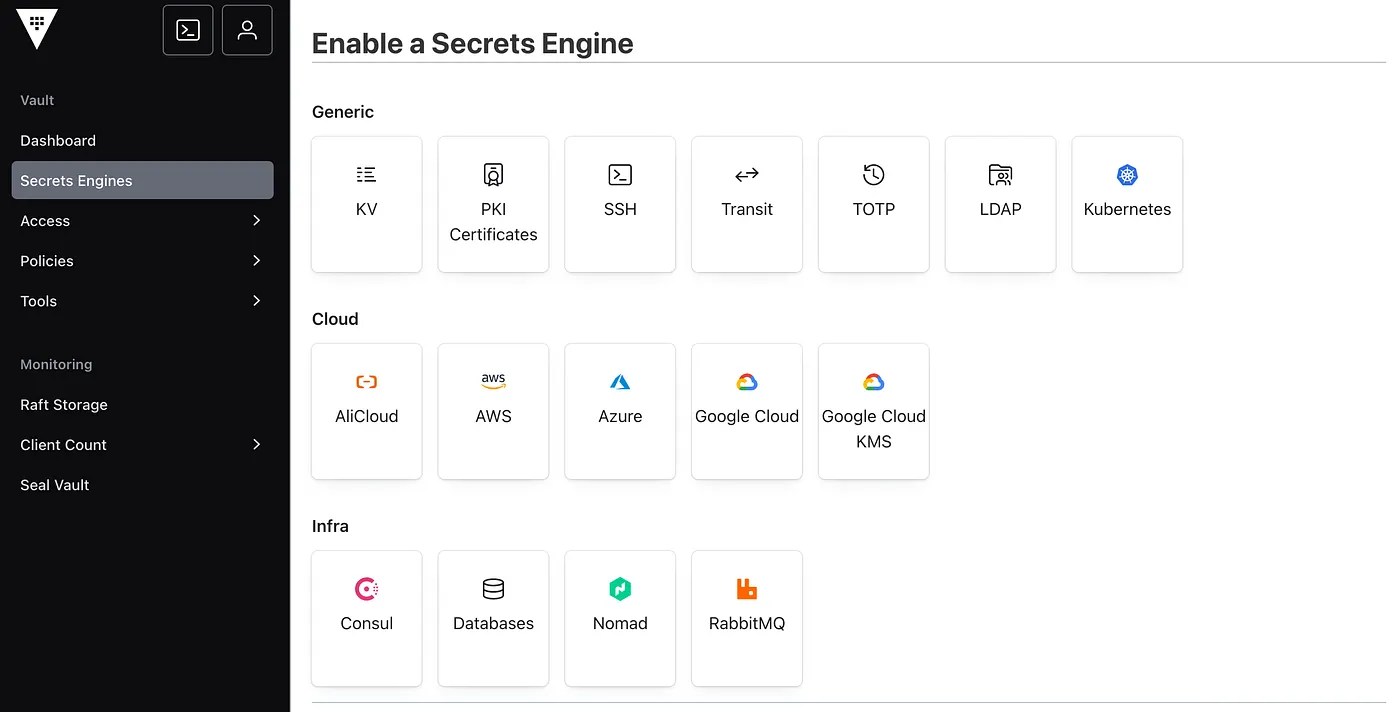
Vault’s main way to access secrets is through the API based on security policies set up in advance. It allows companies to maintain tight and granular access controls and keep thorough audit logs. Vault offers some of the most complex security features on the market.
A web interface is available for secrets management, but it is important to keep in mind that some of Vault’s features are not available in its Web UI (i.e., some of the dynamic secrets functionalities).
While Vault is a feature-rich secrets management tool, it is also extremely complex and has even led to “Vault engineer” being a job title. For instance, (re)starting an HCP Vault cluster always involves one or more operators to unseal it, which adds to operational complexity. HashiCorp Vault mainly works with a token system. Each token is provided to a corresponding policy that may limit the available actions and the paths. Most of that logic needs to be custom-built.
Some other important features of HCP Vault are:
-
Vault is able to generate secrets on-demand (dynamically) for some operations (e.g., PostgreSQL database).
-
HCP Vault is able to set up replication across multiple data centers.
Pros:
-
Vault has one of the most comprehensive and feature-complete secret management solutions on the market and has deep integrations in the IBM ecosystem.
-
HashiCorp Vault is source-available under the BSL license.
Cons:
-
Vault is fundamentally a key-value store and policy engine with workflows, UIs, and automation built on top by the customer.
-
HashiCorp Vault’s pricing is convoluted and is heavily focused on large-scale enterprises.
-
HashiCorp Vault is entirely focused on platform engineering teams. This makes it fairly hard to understand at first, while at the same time it keeps developers out of the secret management workflows. In turn, this may lead to having to build developer tooling on top of Vault in future.
-
HashiCorp Vault is not open source and some companies might have their legal teams not approve HashiCorp’s BSL license.
-
Vault’s free source-available version comes with a very high setup and maintenance costs (in terms of platform engineering team’s time but also compute resources).
-
Operating Vault at scale requires specialized expertise, with larger companies employing 10+ engineers to work on Vault alone.
-
Since the IBM acquisition, customers have reported slower roadmap velocity and longer response times in joint support channels, which is a meaningful concern for teams evaluating long-term fit.
Read more: HashiCorp Vault Alternatives
3. Doppler
Compared to Infisical or Vault, Doppler is a fully closed-source secrets management solution. Similar to Infisical, Doppler is focused on developers and offers a friendly UI dashboard, where developers can modify secret values, set permissions, monitor access logs, and more.
Doppler supports both static secrets and dynamic secrets functionality.
In addition, Doppler also provides a secret sharing product, which allows developers to securely share secrets (e.g., password or any sensitive information) internally.
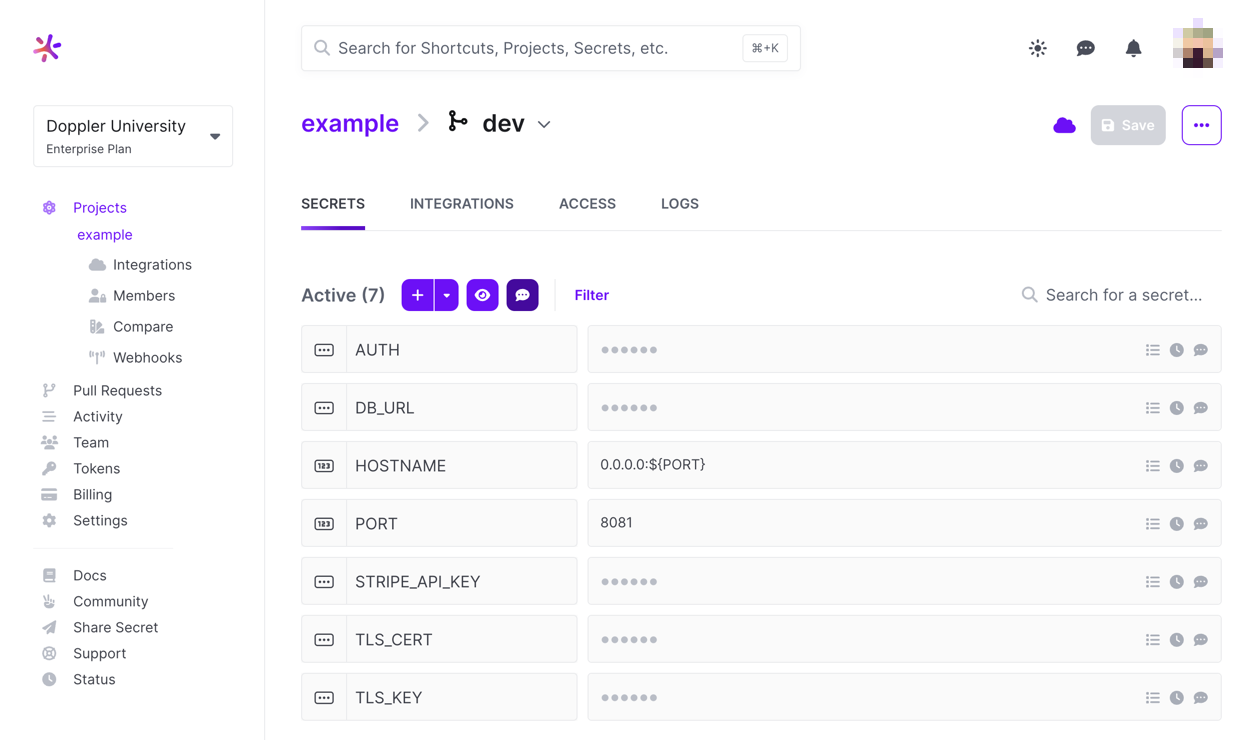
Pros:
-
A simple CLI makes it easy to set up to inject secrets as environment variables.
-
An extensive list of automatic integrations with 3rd-party services and infrastructure tools (e.g., Docker, Kubernetes).
Cons:
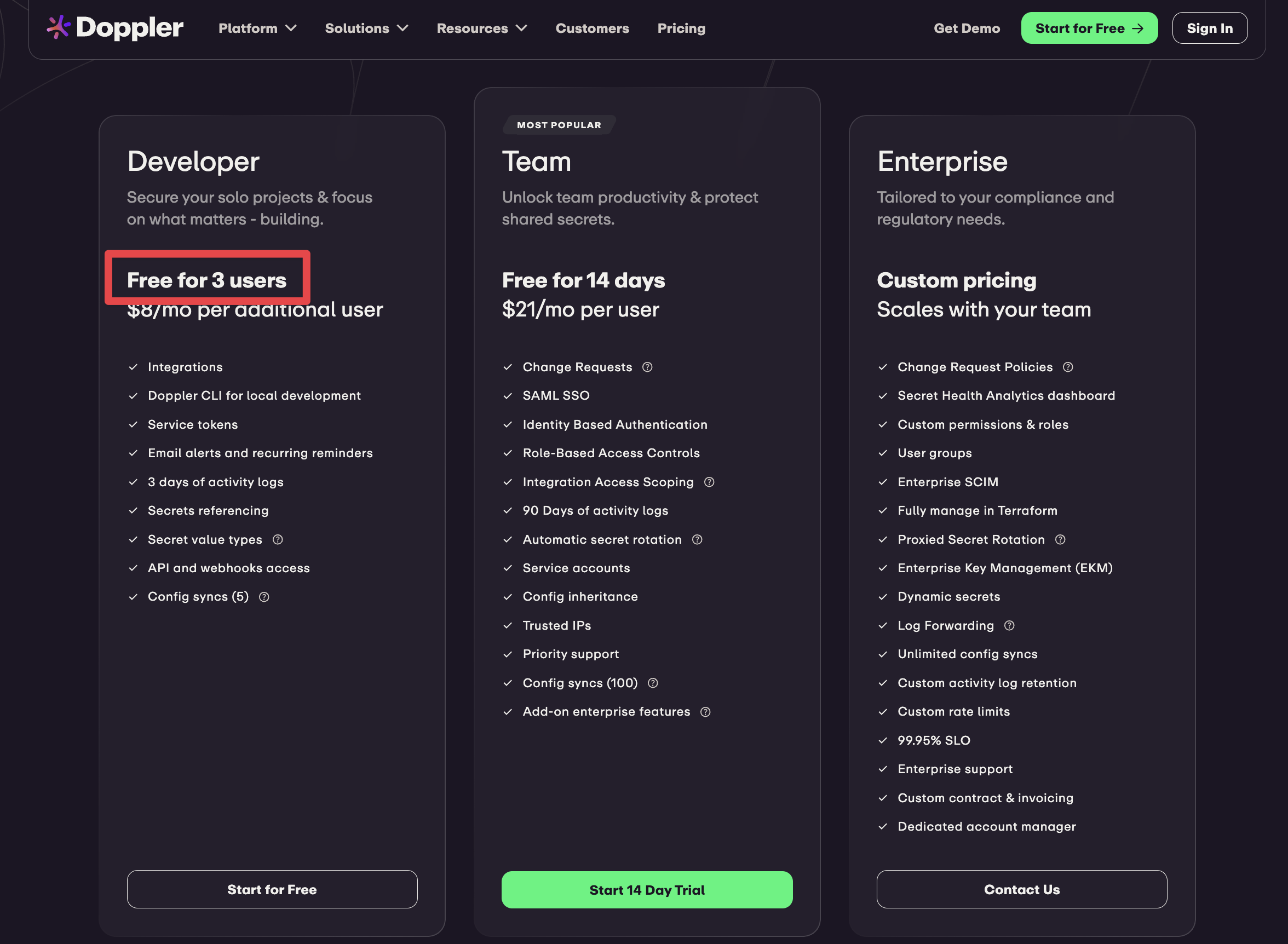
-
Doppler only works as a managed service. It has no open-source version or self-hosting option, which might not satisfy compliance requirements, especially in regulated industries or larger enterprises.
-
Doppler focuses on injecting secrets as environment variables and offers thinner SDKs and fewer integrations than more comprehensive platforms
-
Doppler only offers one organizational layer, which makes it hard to use for multi-tenancy, multi-cloud or other, more complex setups.
-
Doppler’s free plan is limited to three users.
-
The product only offers secrets management, which means other security tools (certificate management, PAM, etc.) need to be purchased separately.
Read more: Doppler Alternatives
Cloud-specific secret managers
Cloud-specific services are typically barebones tools that should only be considered if you’re building applications entirely built on one type of infrastructure.
The benefit is that provider-specific secrets management products directly integrate with your infrastructure, obviating the need for third-party integrations.
The problem with cloud-specific secret managers is that as soon as you run on more than one type of infrastructure, you’re back at square one, manually managing your credentials.
1. AWS Secrets Manager
If your applications are entirely under the AWS stack, AWS Secrets manager is worth evaluating. AWS Secrets Manager is a simple, but resilient solution that lets you rotate, manage, retrieve database credentials, API keys, and passwords.
It handles storage, encryption (via AWS KMS), versioning and rotation. Of course, it integrates natively with services like RDS, Redshift, and Lambda. Cross-region replication and resource-based policies are available for multi-account setups.
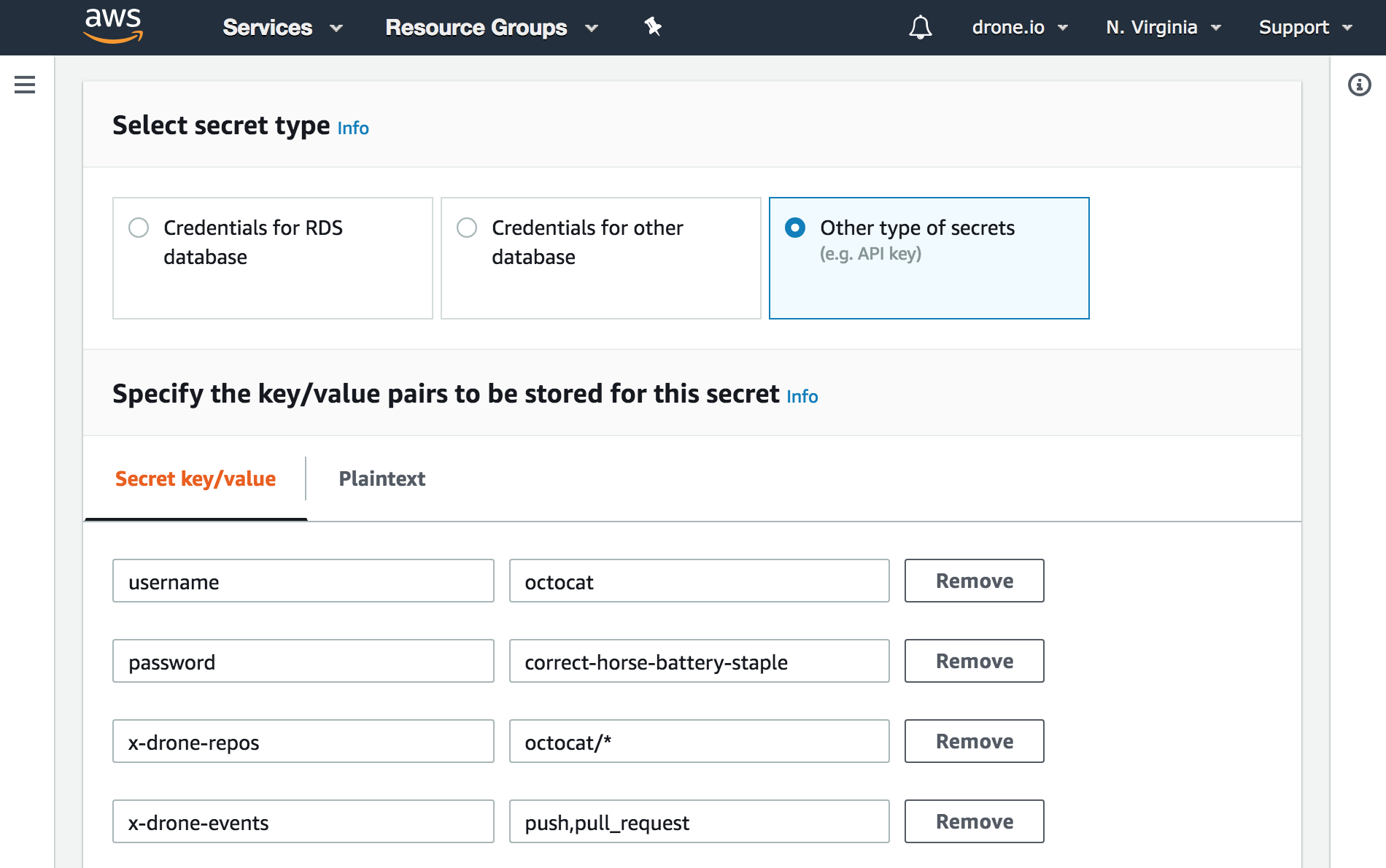
Read more: AWS Secrets Manager Alternatives
Pros:
-
Native managed rotation for AWS databases (RDS, Aurora, Redshift, DocumentDB) without custom code.
-
Built-in cross-region replication that propagates rotated values automatically.
-
Supports external secrets for MongoDB Atlas and Confluent Cloud.
-
Tight integration with AWS KMS, CloudTrail, and IAM.
Cons:
-
Rotating anything outside natively-supported services requires custom Lambda functions.
-
Per-secret pricing scales linearly with agent counts.
-
Third-party integrations often require custom dev work.
-
UI workflows are thin.
-
AWS-only by design. Expanding to multi-cloud later means running a parallel secrets system. The more you've leaned on native rotation and IAM, the harder that migration gets.
2. GCP Secret Manager
If Google Cloud Platform is your cloud provider, GCP Secret Manager could be an option. It includes secret storage with access controls, audit logs, secret versioning and rotation capabilities.
In addition, GCP Secret manager supports a number of ways to access secrets through APIs, client libraries for various programming languages, etc.
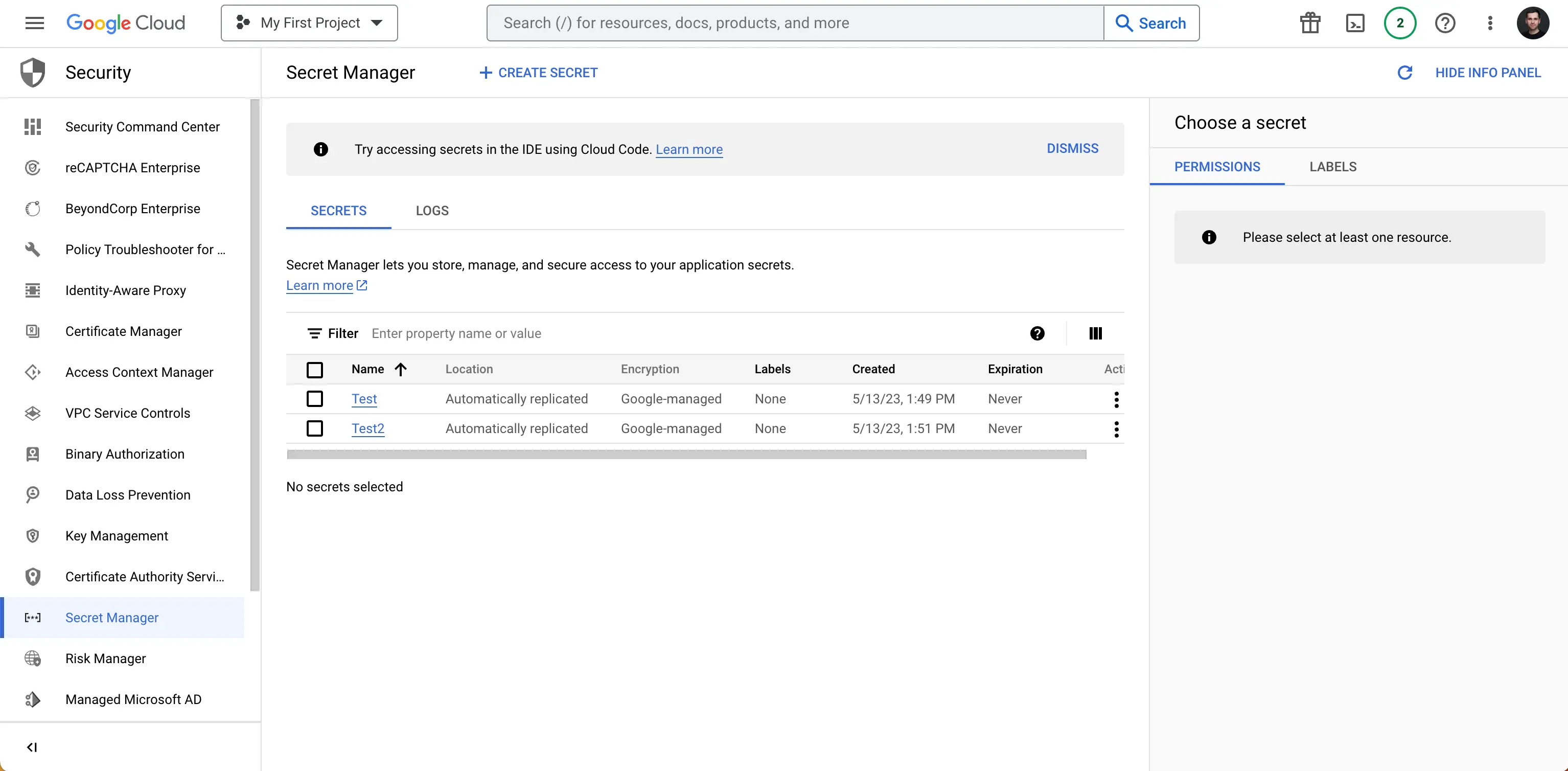
Pros:
-
Generous always-on free tier (six active versions, 10K access operations/month).
-
Your encryption keys stay under your control, data stays within your network boundaries, and services can authenticate each other without managing passwords or credentials.
-
Secrets automatically delete themselves after a set time, changes are safely handled when multiple systems update at once, and your data is automatically copied across regions for reliability.
-
Fine-grained access controls and a full audit trail of who accessed what, and when.
Cons:
- "Rotation" is notification-only. Secret Manager sends you a notification, but you have to write the rotation logic.
- No dynamic secrets engine: it's a static store, not a credential generator.
- At high traffic volumes, you’ll hit the 90k requests/minute limits and individual secrets can’t exceed 64kb. This makes it hard to use at higher scales.
- Over-provisioning is the most common operational pain point.
- GCP-only by design. Patterns don't translate to other clouds, so multi-cloud expansion means rebuilding both the store and the access model.
Read more: GCP Secret Manager Alternatives
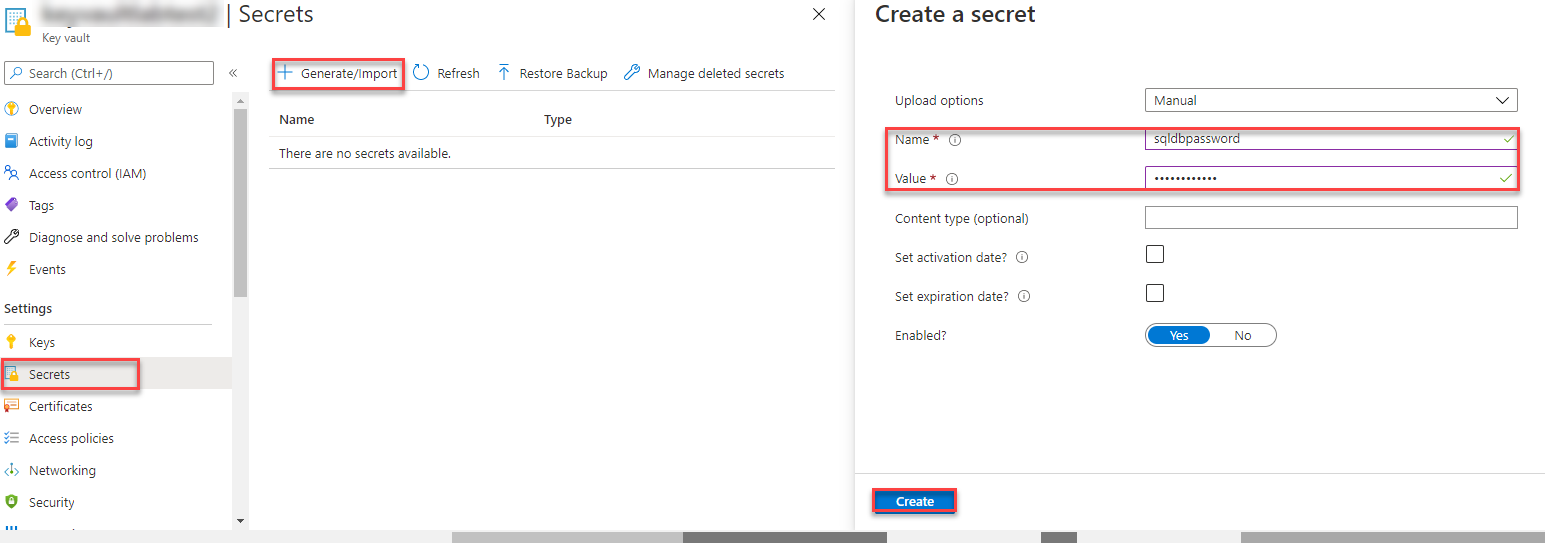
3. Azure Key Vault
If your software and applications run on Azure, Microsoft provides a managed service called Azure Key Vault that lets you manage your secrets in a single repository. This includes keys, certificates, connection strings, and passwords. You can also create and import encryption keys into Azure Key Vault and automate SSL/TLS certificate renewal to ensure secure connections.
For organizations invested in the Azure ecosystem, Azure Key Vault provides a comprehensive pricing model with different tiers for managing secrets, keys, and certificates.
Pros:
- Wider coverage than AWS or GCP. It handles secrets, encryption keys, and SSL/TLS certificates, including automatic renewal.
- If you accidentally delete something, you have between 7 and 90 days to recover it before it's gone for good.
- Higher-security tier stores keys in dedicated hardware. Standard tier uses software protection at lower cost.
- Services running inside Azure can authenticate themselves automatically.
Cons:
- Stores secrets, but won't generate them for you.
- Works smoothly inside Azure, but awkward everywhere else. CI/CD pipelines running outside Azure need workarounds.
- Heavy traffic can get throttled, and vault names share a single global pool. Your preferred name might already be taken.
- Costs can creep up unexpectedly at scale, which comes up repeatedly in user feedback.
- Fully dependent on Azure. Moving away or expanding to other clouds means rebuilding.
Read more: Azure Key Vault Alternatives
Open source projects
There is a variety of open-source secret management products. The main benefit of an open-source secrets management alternative is that they easily pass compliance checks because they can be self-hosted on any infrastructure. Infisical and Vault also check this box, but not all other providers do.
Cost may seem like another benefit (after all, open-source software is free to use). However, maintaining a critical solution like a secrets manager can consume significant resources and make the tool expensive to operate, even if no license fee is paid.
With most open-source projects, no party bears responsibility for maintaining it, fixing bugs, and releasing security patches. Open-source maintainers often do these things, but it’s risky to rely on a solution you do not own.
In addition, none of the following open-source products have a managed service available, meaning self-hosting (and maintaining) is the only option.
1. SOPS
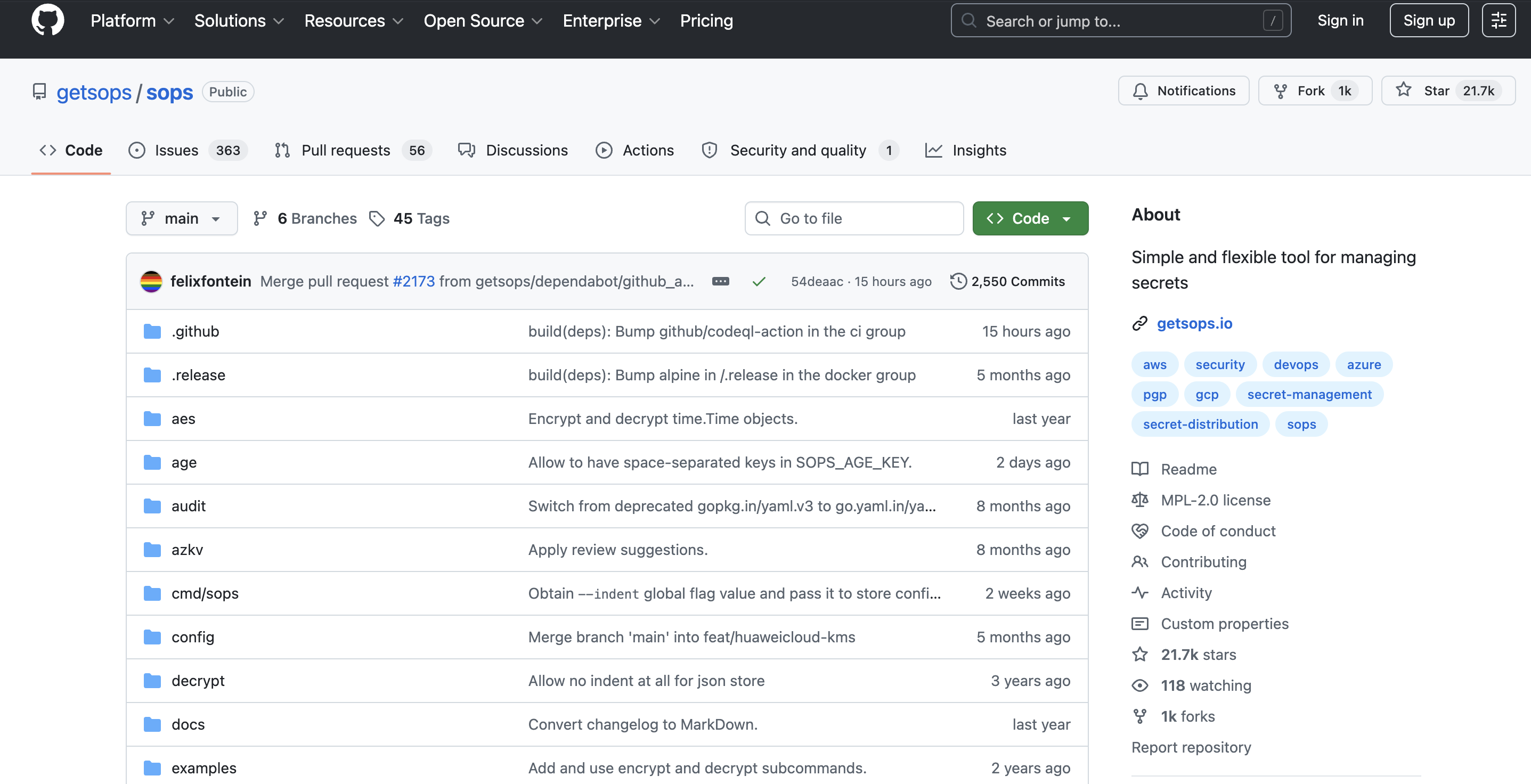
SOPS, which is created by Mozilla, is a popular open-source secret management tool.
Unlike tools like Infisical, which inject secrets at runtime, SOPS lets users securely commit secrets to git repositories. Developers can use Mozilla’s SOPS CLI to encrypt Kubernetes secrets with AWS KMS, GCP KMS, Azure Key Vault, and OpenPGP. SOPS supports file formats like .yaml, .json, .env, and .ini.
SOPS is based on a client-server model for encryption and decryption of the data keys. In the default setting, it runs a local key service within the process. The client sends encryption and decryption requests to the key service using protocol buffers and gRPC.
It should be noted that the key service connection currently does not provide authentication or encryption capabilities. To ensure proper security levels, it is highly recommended to authenticate and encrypt the connection through other means such as SSH tunnels.
Finally, SOPS is able to generate audit logs for files in the specified environments. It records the activity (e.g., timestamps, usernames, file data) in a PostgreSQL database.
Pros:
-
Actively maintained under CNCF stewardship.
-
Lightweight, no server infrastructure to operate, integrates cleanly with Git-based workflows.
-
Broad encryption backend support, including modern age and SSH-key-based encryption.
Cons:
-
Secrets-in-Git is a pattern that doesn’t fit every threat model. Encrypted or not, some teams don’t want sensitive material in version control.
-
No web UI, no centralized policy engine, no audit logs out of the box. Operational visibility has to come from the encryption backend.
-
Best for static secrets and config, not a fit for dynamic secrets, PKI, or PAM use cases.
2. OpenBao
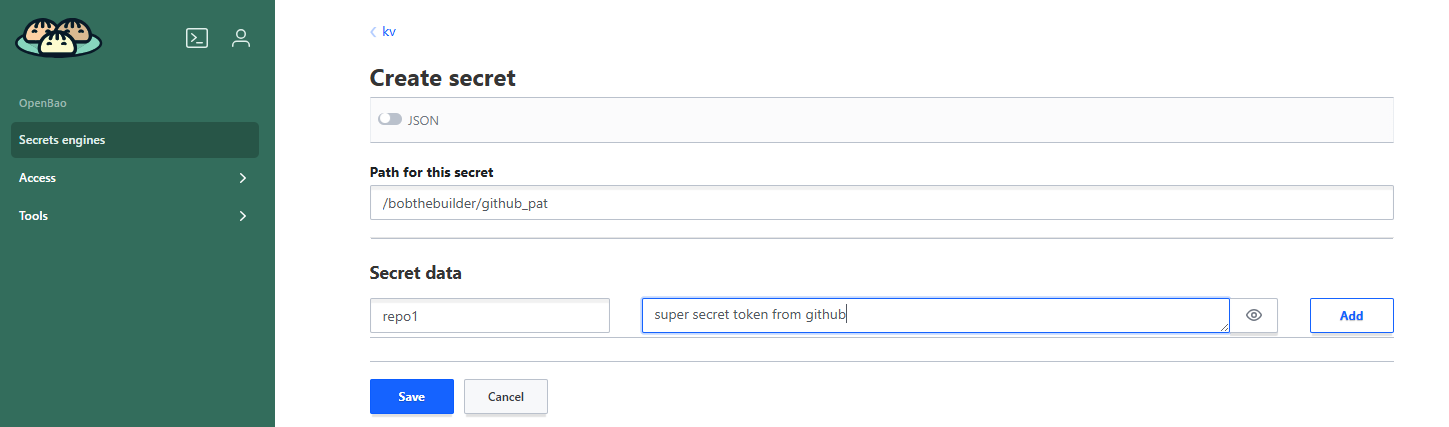
OpenBao is a community-driven fork of HashiCorp Vault, created in late 2023 after HashiCorp moved to the Business Source License.
The fork was taken from Vault v1.14.0 (the last MPL-licensed release) and is now governed by the Linux Foundation and OpenSSF, with IBM engineers among the major contributors.
OpenBao maintains API compatibility with Vault and is frequently updated by maintainers that include IBM engineers. For teams that want Vault’s architecture and feature set, OpenBao is a credible open-source path.
Pros:
-
True open-source license (MPL 2.0) with no commercial-use restrictions.
-
Linux Foundation / OpenSSF governance with a multi-vendor stewardship rather than a single company.
-
API-compatible with Vault, which simplifies migration paths.
Cons:
-
Inherits Vault’s operational complexity. Same Raft cluster management, same key-value-store-as-foundation pattern, same need for custom workflows and UI work.
-
Younger project so production deployments at scale are still less common than for Vault itself.
-
No managed service offering: self-hosting is the only option.
3. Other alternatives
There are a few secrets managers that started as internal tools their creators open-sourced: Confidant by Lyft, Keywhiz by Square, Chamber by Segment and Knox by Pinterest. These were built primarily for their authors’ internal infrastructure and have varying degrees of life left in them.
Confidant was archived by Lyft on April 17, 2025, and is read-only. Keywhiz and Knox are still on GitHub but show minimal activity. None of these are reasonable secrets management tools for new deployments.
Bitwarden Secrets Manager is a recent entrant. It’s open-source, with client-side encryption and self-hosting available on enterprise plans. It’s a legitimate option for teams already in the Bitwarden ecosystem.
Building in-house
Some teams decide to build secrets management in-house, especially as resources grow and requirements become distinct.
There are, however, a few considerations to keep in mind:
-
Building something as critical as secrets management in-house creates large engineering overhead. Staying up to date on the latest third-party APIs and defending against new attack vectors requires constant effort from a dedicated team of developers that could be working on the core product.
-
Companies like Infisical spend nearly all of their time thinking about compliance and security. This helps prevent most things that could go wrong (Or, in the case of secret rotations, offers quick remedies). In-house squads rarely have this deep expertise or learning from hundreds of companies.
Key considerations for selecting the right secrets management tool
Choosing the right secrets management solution to follow best security means understanding your needs and requirements.
Cloud-specific secret managers are only viable If your stack is built entirely in one of the major clouds’ ecosystems (i.e. AWS, GCP, Azure). If your infrastructure is (or might be) multi-cloud in the future, these tools might signal a costly migration in the future.
For extremely tight budgets, fully open-source projects like OpenBao and SOPS are a great fit. They may be complex to operate and consume development resources, but they’re ultimately free.
If you don’t mind investing in dedicated engineering capacity and dealing with some complexity (but getting a mature secrets manager) and price is less of a consideration (The cheapest production-grade option starts at roughly $1,152/month before client fees), Vault may be the best tool for you.
If you care deeply about developer experience and efficiency of your core and platform engineering teams, Infisical is the best. With options to expand into PKI and PAM without switching providers and a sleeker way to operate (without losing hosting flexibility) Infisical is likely the right choice for most teams that want both a feature-rich security suite and ease of use. You can try the product for free (including a free trial of the paid Pro tier) or book a demo to see how it fits in your instance.