Navigating the complexities of API key management is essential for robust security and seamless system performance. This article focuses exclusively on best practices, common challenges, leading devtools (e.g, Infisical), and the importance of proficient API key management.
What is API key Management?
API key management refers to the processes and methodologies involved in secure handling, storage, and usage of API keys to access third-party tools and services. When integrating external APIs into applications, managing these keys effectively is crucial to ensure security, maintain functionality, and comply with the service's usage policies. Key aspects include:
-
Secure Storage: Storing API keys securely to prevent unauthorized access. This often means keeping them out of code repositories and using secure storage solutions like environment variables, encrypted databases, or dedicated secrets management services.
-
Access Control: Limiting who can access and use the API keys within your organization. This involves setting up proper roles and permissions to ensure only authorized personnel can retrieve and use the keys.
-
Usage Monitoring: Keeping track of how and where the API keys are used. Monitoring helps in identifying unusual patterns that might indicate a security issue or a breach of the third-party service's usage policies.
-
Rotation and Renewal: Regularly updating or rotating API keys, especially if there's a suspicion of compromise or as a routine security practice. This helps in minimizing the window of opportunity for any misuse if a key is compromised.
Proper management of API keys used for external services is essential to protect your application from security breaches, data leaks, and service disruptions, ensuring a smooth and secure integration with third-party APIs. One of the solutions
Why is API key Management So Important?
Effective management of API keys used for external services is paramount, as these keys serve as gatekeepers to critical functionalities and sensitive data. A compromised API key can lead to unauthorized access, data breaches, or service interruptions, posing significant risks to an organization's security, reputation, and legal standing.
Properly handling these keys safeguards against such vulnerabilities, ensuring secure and uninterrupted access to essential third-party services. Moreover, it ensures compliance with service agreements, preventing overuse or misuse of APIs that could result in costly penalties or service denials. In essence, diligent API key management is a cornerstone of maintaining the integrity, reliability, and security of an organization's digital infrastructure.
Best Practices for Effective API key Management
1. Prioritize Encryption of API keys
- Encryption at Rest and in Transit: Always encrypt api keys, not only when they are stored (at rest) but also when they are being transmitted (in transit). This dual-layer of encryption protects against different types of potential breaches.
- Implementing Strong Encryption Standards: Use industry-standard encryption algorithms and regularly update them to ensure they remain secure against emerging threats.
2. Implement Rigorous Access Control
- Principle of Least Privilege: Grant access to api keys strictly on a need-to-know basis. Only individuals whose roles require access to specific secrets should have it, and their level of access should be the minimum necessary for their tasks.
- Regular Review and Revocation of Access Rights: Periodically review who has access to what secrets and revoke access that is no longer needed, especially when employees change roles or leave the organization.
3. Conduct Regular Auditing and Monitoring
- Audit Trails: Maintain comprehensive logs of when and how api keys are accessed. This helps in tracking unauthorized access, preventing secret sprawl, and understanding the context of legitimate access.
- Real-time Monitoring: Implement systems that can monitor api keys access in real-time and alert administrators to unusual patterns that might indicate a security threat.
4. Implement Routine Rotation of Secrets
- Scheduled Secret Changes: Regularly change api keys to reduce the risk of them being compromised. This practice is especially important for highly sensitive systems or in the aftermath of a security incident.
- Automated Secret Rotation: Where feasible, use automated tools (e.g., Infisical) to rotate api keys and generate dynamic keys, which reduces the potential for human error and ensures timely updates.
How does API key Management relate to Secret Management?
In the broader context of corporate cybersecurity, API keys are just one part of an overarching secrets management strategy. This strategy covers everything from passwords and encryption keys to SSH keys, authorization tokens, and private certificates. Managing these secrets involves setting and enforcing policies to ensure they are well-protected, both when stored and during transmission.
The life cycle of a secret, including API keys, starts with its creation and moves into regular use. While in use, it's crucial to regularly rotate or change these secrets to prevent unauthorized access, similar to how regularly updating passwords helps maintain security. Once a secret has reached the end of its life cycle, it's retired or revoked, making it unusable for any future attacks.
APIs, which allow different parts of a system or external services to communicate, highlight the need for robust secrets management. Ensuring strong API key security is part of maintaining a secure, well-rounded secrets management system. This comprehensive approach doesn't just protect individual pieces of sensitive information; it strengthens the entire organization's defense against cyber threats.
Tools to Aid with API key Management
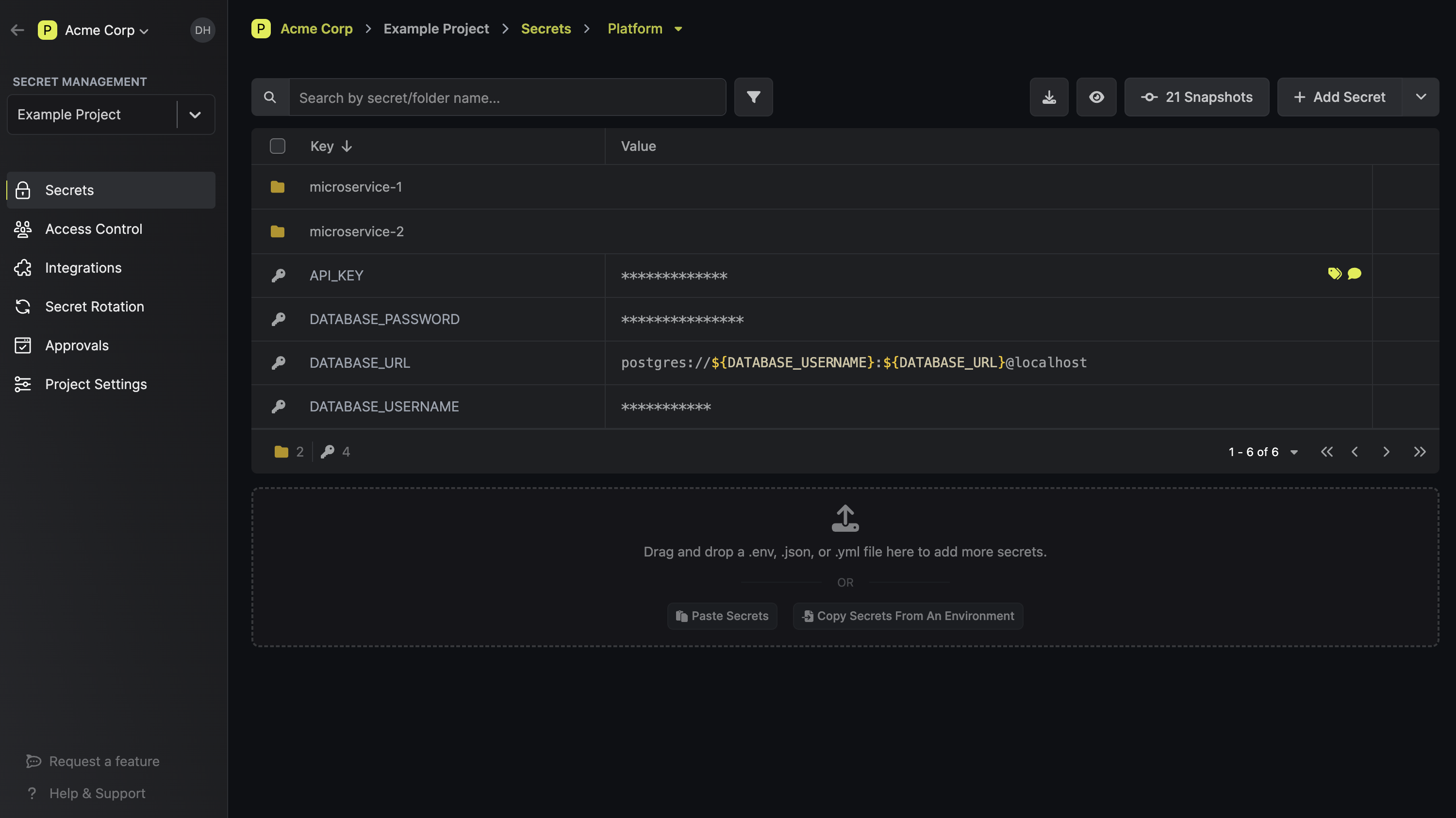
In the realm of secret management, there are various tools (commonly called "vaults") offering robust solutions to safeguard sensitive digital credentials. Among these, Infisical is an open source secrets management platform. It emerges as a noteworthy solution, particularly for its user-friendly experience and advanced security features. It specializes in providing a highly secure environment for storing and managing api keys with an emphasis on ease of use and integration flexibility. This makes Infisical an excellent API key manager for organizations looking for a balance between advanced security and user accessibility in their api key management practices.